In This Issue:
In this week’s issue, you’ll find information regarding the most current critical threats and preventative measures to lessen the chances of a breach.
- Apple Vishing Scam
- Banking Trojan Emotet Is Back In A New Form
- Authentication Flaw Found In Cisco SOHO Switches
- Linux APT Flaw
- Phish Tale of the Week
- How Can Netizen help?
Apple Vishing Scam
There is a new vishing (phone phishing) scam that people are encountering that spoofs official Apple Inc phone numbers. Automated calls are going out that look official on people’s phones, displaying Apple’s logo, address, and real phone number, and warning people that there has been a data breach at Apple. The interesting, and scary, part is that the phone call is indistinguishable from legitimate calls to and from Apple in the phone’s recent calls list.
If someone picks up this scam call, they would hear that multiple servers containing Apple user IDs have been compromised and to call back to a 1-866 number which definitely doesn’t belong to Apple. If the number is called, you would hear an automated system answer telling you that you’ve reached Apple support and your expected wait time. You’d then hear a non-English speaker, likely someone from India, ask you about your call reason.
This is almost certainly a scheme to get unsuspecting people to divulge their personal and/or financial details, using the frightening tail of your information having been stolen. The fact that iPhones can’t tell the difference between a scammer spoofing Apple’s number and a legitimate one is worrying, as many people might fall prey to this clever tactic.
Recommendations:
Knowledge about these types of scams in the first place helps immensely. If you get a seemingly official looking call from a company you know where they are asking for personal and/or financial details, hang up, find the official company number from the company’s website and call them back. Don’t rely on a search engine result to tell you, as scammers have been polluting search results to get their numbers to appear and seem more legitimate.
Banking Trojan Emotet Is Back In A New
Companies are on alert as the infamous Emotet Trojan has emerged on the cybersecurity radar ready to cause damage. What is Emotet? It is an advanced, modular banking Trojan that primarily functions as a downloader or dropper of other banking Trojans. This Trojan was first discovered in 2014 and was originally designed to sneak onto you computer and seal sensitive and private information. Later versions of the software saw the addition of spamming and malware delivery services including other banking Trojans.
How does the Emotet Trojan spread? It is usually spread through SPAM emails using a malicious script, a macro-enabled document file (like a Word attachment), or a malicious link. These emails will look very legit containing familiar branding designed to look like a legitimate email. Emotet may try to persuade users to click the malicious files by using tempting language about “Your Invoice,” “Payment Details,” or possibly an upcoming shipment from well-known parcel companies. Once it is downloaded to a victims computer it turns into an almost worm-like malware and starts spreading on the network and also starts installing other Trojans to the infected machine. It will also ransack your contact lists and send itself to your friends, family, coworkers and clients. Since these emails are coming from your hijacked email account, the emails look less like spam and the recipients, feeling safe, are more inclined to click bad URLs and download infected files. Finally, if a connected network is present, Emotet spreads using a list of common passwords, guessing its way onto other connected systems in a brute-force attack. If the password to the all-important human resources server is simply “password” then it’s likely Emotet will find its way there.
Why is Emotet coming back? Emotet is coming back by bypassing SPAM email detectors. How it does this is the Trojan is polymorphic. What this means is that every time the Trojan is downloaded it changes itself to evade signature-based detection. Moreover, Emotet knows if it’s running inside a virtual machine (VM) and will lay dormant if it detects a sandbox environment. Emotet also uses C&C (Command & Control) servers to receive updates. This works in the same way as the operating system updates on your PC and can happen seamlessly and without any outward signs. This allows the attackers to install updated versions of the software, install additional malware such as other banking Trojans, or to act as a dumping ground for stolen information such as financial credentials, usernames and passwords, and email addresses.
Why Should I be Worried? Emotet can attack anyone and has no specific target list. To date, Emotet has hit individuals, companies, and government entities across the United States and Europe, stealing banking logins, financial data, and even Bitcoin wallets. One close and noteworthy Emotet attack occurred on the City of Allentown, PA and required direct help from Microsoft’s incident response team to clean up and reportedly cost the city upwards of $1M to fix. However, on this most recent addition of the virus no activity is currently being detected in Russia which indicates that the attackers are likely not based in Russia.
Recommendations:
- Keep your computer/endpoints up-to-date with the latest patches for Microsoft Windows. Emotet may rely on the Windows EternalBlue vulnerability to do its dirty work, so don’t leave that back door open into your network.
- Don’t download suspicious attachments or click a shady-looking link. Emotet can’t get that initial foothold on your system or network if you avoid those suspect emails. Take the time to educate your users on how to spot mailspam.
- Educate yourself and your users on creating a strong password. While you’re at it, start using two-factor authentication.
- You can protect yourself and your users from Emotet with a robust cybersecurity program that includes multi-layered protection.
Authentication Flaw Found in Cisco SOHO Switches
A critical and unpatched vulnerability was found in the popular Cisco Small Business Switch software that leaves remote, unauthenticated attackers gaining full administrative control over the device.
The vulnerability (CVE-2018-15439) which was found to have a Common Vulnerability Scoring System (CVSS) severity score of 9.8, was found due to the default configuration on the devices include a default, privileged admin user account that is used for initial login of the device, and can not be removed. The account may be disabled but only after another user account is created with the same privilege level. Once that additional account is removed, the system automatically re-enables the default privileged account without any form of notification to system administrators.
As these switches are used to manage a LAN, an exploit means that the remote attacker would be able to gain access to network security functions such as firewalls, or management interfaces for administrating data and wireless connectivity or VOIP network devices.
Cisco has advised that “Under these circumstances, an attacker can use this account to log into an affected device and execute commands with full admin rights.” adding that “It could allow an unauthenticated, remote attacker to bypass the user-authentication mechanism of the affected device.”
Currently, no patch that addresses the current vulnerability is available. However, Cisco says a patch is expected to be released the future; for now, users can address the vulnerability by configuring an account using admin as user ID, setting the access privilege to level 15, and defining the password by replacing <strong_password> with a complex password chosen by the user, according to the advisory. By adding this user account, the default privileged account will be disabled. Make certain to record and secure the password for this Switch device.
Linux APT Flaw
Security research has revealed a critical remote code execution flaw in Linux APT. Vulnerability dubbed CVE-2019-3462 is within the APT package manager; an extremely popular utility and tool when it comes to installation, updates, and upgrades, and the removal of software on many flavors of Linux distributions including Debian and Ubuntu. The issue lies with APT’s failure to sanitize particular parameters during HTTP redirects; this failure opens up the potential for a man-in-the-middle (MiTM) attack in which the attacker can inject malicious content and trick the host system into installing tampered packages.
HTTP redirects are utilized in APT, specifically the “apt-get” command, to help Linux machines to automatically request packages from proper mirror servers where others may not be available for distribution. In short, if one source fails to respond, the APT will then redirect or respond with another location of the next available source where the client should request the desired package. Not only would the attacker be able to insert themselves in the middle with a malicious mirror and execute arbitrary code, but they could do so with the highest level of privileges (i.e., root). While it has not been confirmed, it is possible that this vulnerability affects all package downloads, whether it be a new package or updating an old one.
Recommendations:
APT has since released a patch for the flaw in patch number 1.4.9. So it is imperative that systems be updated as soon as feasible, while also considering some other layers of security:
- Utilize signature-based verification to protect the integrity of packages.
- Implement HTTPS to prevent active exploitation (HTTP with SSL/TLS Encryption).
Phish Tale of the Week

The phishing email this week claims to be a OneDrive email that was sent from a Xerox multi-function printer. Not only is the sender suspect, but closer examination of the “View Document” link shows an unknown malicious site.
Recommendations:
A phishing email will typically direct the user to visit a website where they are asked to update personal information, such as a password, credit card, social security, or bank account numbers. A legitimate company already has this sensitive information and would not ask for it again, especially via email.
- Scrutinize your emails before clicking anything. Did you order or ask for anything for which you’re expecting a confirmation? Did the email come from a store you don’t usually order supplies from or a service you don’t use? If so, it’s probably a phishing attempt.
- Verify that the sender is actually from the company sending the message.
- Did you receive a message or email from someone you don’t recognize? Are they asking you to sign into a website to give Personally Identifiable Information (PII) such as credit card numbers, social security number, etc. A legitimate company will never ask for PII via instant message or email—this is a huge red flag.
- Do not give out personal or company information.
- Review both signature and salutation.
- Do not click on attachments.
- Do not click on unrecognized links. If you do proceed, verify that the URL is the correct one for the company/service and it has the proper security in place, such as HTTPS.
- Be wary of poor spelling, grammar, and formatting. As can be seen with the with this email, there are multiple spelling, grammar, and formatting errors, leading us to believe that the message is illegitimate. If an email is visually unprofessional, the sender is likely not who they say they are.
Many phishing emails pose a sense of urgency or even aggressiveness to prompt a form of intimidation. Any email requesting immediate action or that is addressing you in a threatening manner should be questionable. Also, beware of messages that seek to tempt users into opening an attachment or visiting a link. For example, an attachment titled “Staff Pay Raises 2018” may seem like something you really want to know about, but it could just be a ploy to plant malware on your system or steal your credentials.
How Can Netizen Help?
Netizen ensures that security gets built-in and not bolted-on. Providing advanced solutions to protect critical IT infrastructure such as the popular “CISO-as-a-Service” wherein companies can leverage the expertise of executive-level cybersecurity professionals without having to bear the cost of employing them full time.
We also offer compliance support, vulnerability assessments, penetration testing, and more security-related services for businesses of any size and type.
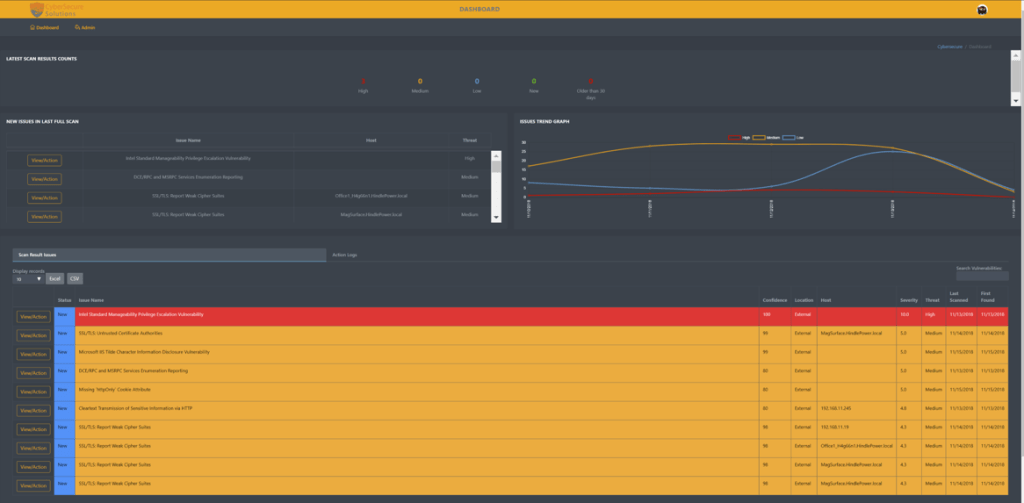
Additionally, Netizen offers an automated and affordable assessment tool that continuously scans systems, websites, applications, and networks to uncover issues. Vulnerability data is then securely analyzed and presented through an easy-to-interpret dashboard to yield actionable risk and compliance information for audiences ranging from IT professionals to executive managers.
Netizen is an ISO 27001:2013 (Information Security Management) certified company.