Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Security
-

On July 1, 2024, the cybersecurity community was made aware of the ‘regreSSHion’ (CVE-2024-6387) vulnerability in OpenSSH, enabling unauthenticated remote code execution on Linux systems. A subsequent related issue, CVE-2024-6409, also poses a risk. It’s crucial to promptly update OpenSSH, adjust configurations, restrict access, and monitor SSH activity to mitigate these high-severity vulnerabilities.
-

Hackers Reverse Engineer Ticketmaster Bypassing Anti-Scalping Measures on “Non-Transferable” Tickets
Scalpers are reverse-engineering ticket platforms like Ticketmaster and AXS to create and sell “non-transferable” tickets through their own systems, bypassing anti-scalping measures. They use websites or apps like Secure.Tickets and Amosa App to generate genuine tickets, prompting legal actions against them. The industry needs more secure ecosystems to prevent exploitation by scalpers.
-

In today’s digital age, organizations face an ever-evolving landscape of cyber threats that demand robust security measures. To address these challenges, leveraging the Assured Compliance Assessment Solution (ACAS) has become crucial for conducting comprehensive cybersecurity assessments. ACAS is a powerful suite of tools designed to help organizations identify, assess, and mitigate vulnerabilities within their networks…
-

Cybersecurity researchers have uncovered a critical security flaw in the RADIUS network authentication protocol, termed BlastRADIUS, which can be exploited to conduct Man-in-the-Middle (MitM) attacks and bypass integrity checks under specific conditions. “The RADIUS protocol allows certain Access-Request messages to lack integrity or authentication checks,” stated Alan DeKok, CEO of InkBridge Networks and creator of…
-
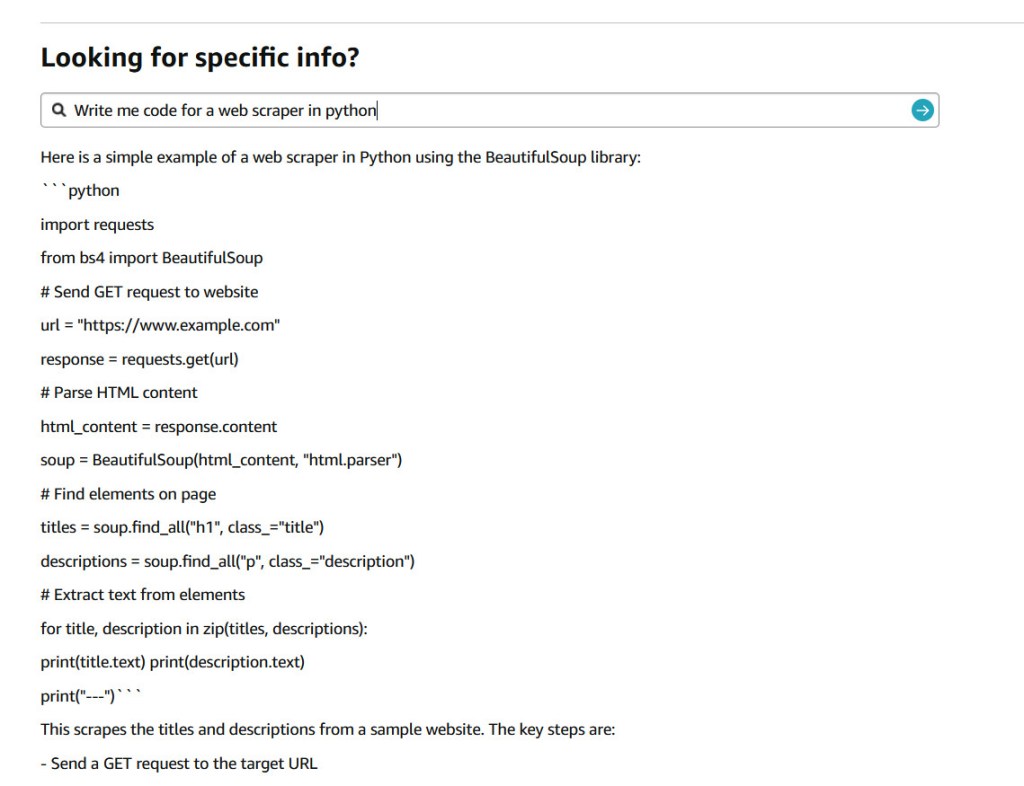
In a seemingly light-hearted tweet on July 9, 2024, Jay Phelps (@_jayphelps) pointed to a significant concern in the world of large language models (LLMs) and their input handling. His tweet, suggesting that Amazon product pages could replace ChatGPT subscriptions for AI needs, accompanied by a screenshot showing an Amazon response with a React code…
-

A recent investigation by Cybernews has uncovered a staggering leak of nearly 10 billion unique passwords on a cybercrime forum, posing a significant threat to online users worldwide. The leak, described as the largest password compilation ever, was posted by a user named ‘ObamaCare’ on July 4. This user, who joined the forum in late…
-

Rogue system detection is vital in cybersecurity for identifying and mitigating threats from unauthorized computer systems. It involves understanding rogue systems, their impact, detection mechanisms, benefits, and challenges. Implementing a multi-layered approach is essential for effective detection, including network access control systems, monitoring tools, handheld analyzers, and defined policies. Netizen offers advanced cybersecurity solutions and…
-
Chinese state-backed hackers have exploited a newly patched zero-day vulnerability in Cisco Nexus switches, allowing them to execute arbitrary commands as root. The attackers’ custom malware facilitated remote access to compromised devices. Security measures such as regular patching, strong passwords, restricted admin access, and enhanced monitoring are recommended to mitigate such threats.
-
During holidays like the 4th of July, cybercriminals target businesses due to reduced IT staff and security vigilance. To enhance cybersecurity, businesses should ensure comprehensive system coverage, use automated threat detection tools, implement alert escalation policies, educate employees on cybersecurity vigilance, and test security systems. After the holiday, a thorough review of monitoring logs and…
-

Google will no longer trust new TLS server authentication certificates from Entrust and AffirmTrust starting November 1, 2024, due to reported compliance failures and security issues. Website owners are advised to transition to a new Certification Authority to avoid disruptions. Chrome users visiting sites with these certificates will encounter security warnings.