Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Security
-

This content covers phishing tactics targeting Amazon users, EU scrutiny of Meta, and a federal recovery from a CrowdStrike outage. It advises caution with unsolicited links and attachments, scrutinizing messages, and not divulging personal information online. It also highlights Netizen’s cybersecurity solutions including CISO-as-a-Service and vulnerability assessments.
-
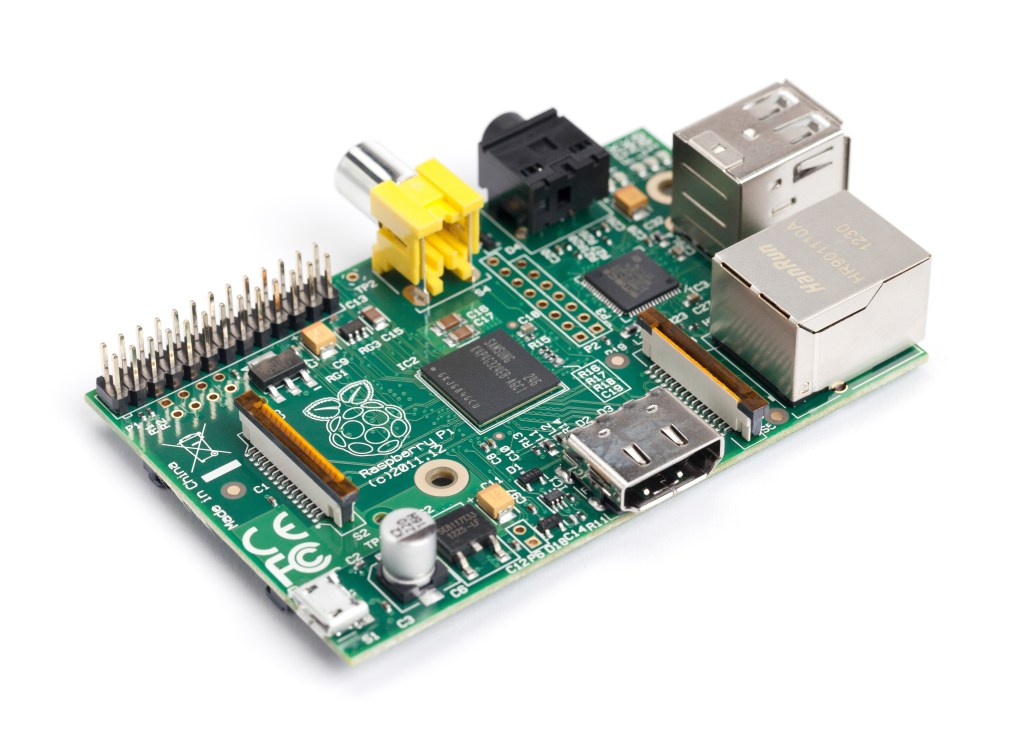
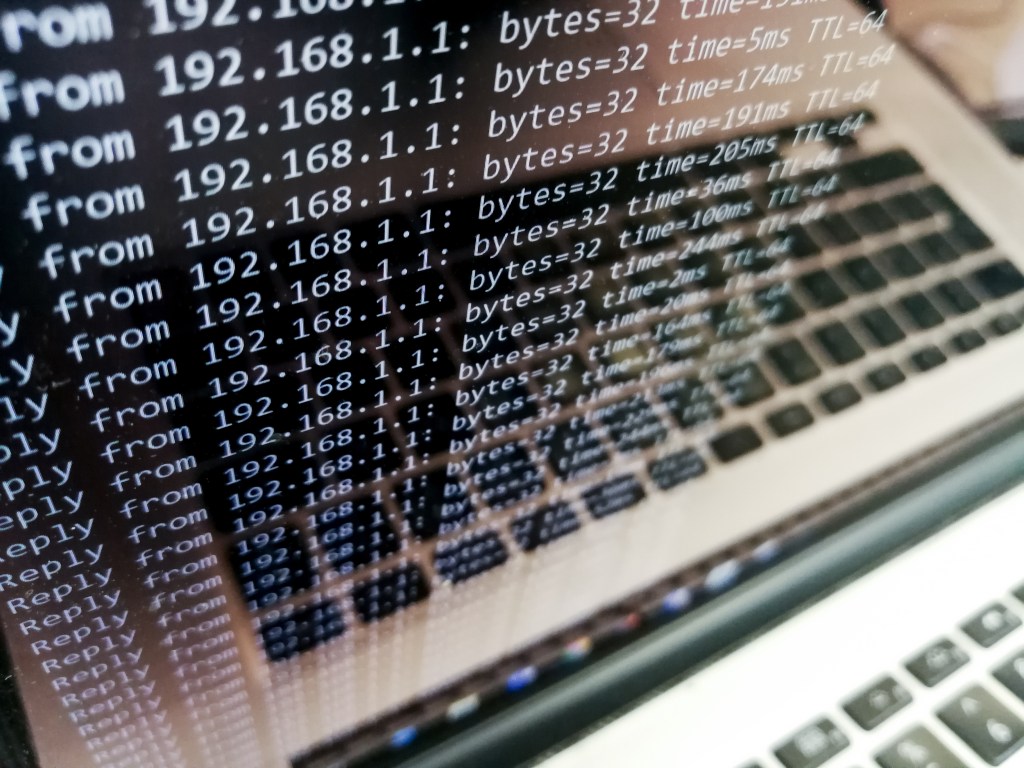
Penetration testing is a flexible skill for cybersecurity analysts. A drop box, like the one built with a Raspberry Pi 3 and TP-Link AC1300 Wi-Fi adapter, provides secure, cost-effective, and easy network access. Netizen offers cybersecurity services, including penetration testing, vulnerability assessments, and automation tools. Visit www.netizen.net/contact for inquiries.
-

A newly discovered vulnerability in Microsoft 365 Copilot highlights how attackers can leverage advanced techniques, such as prompt injection and ASCII smuggling, to exfiltrate sensitive user data. This issue has raised serious concerns in the cybersecurity world, especially considering the rapid integration of AI tools into enterprise environments. The Exploit Breakdown This vulnerability, disclosed to…
-

The FBI’s shortcomings in securing sensitive storage media were exposed in an OIG audit, indicating improper handling and storage of decommissioned devices. Meanwhile, Pavel Durov, CEO of Telegram, was arrested in France for alleged failure to moderate criminal activities on the platform.
-

SOC 2 (System and Organization Controls 2) is a security framework developed by the American Institute of Certified Public Accountants (AICPA). It outlines the criteria for managing customer data based on five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. SOC 2 compliance is critical for organizations that handle sensitive customer information, ensuring…
-
DDoS attacks are a significant threat to internet security that disrupt normal traffic by overwhelming servers. Identifying and mitigating DDoS attacks is crucial. Detection involves monitoring traffic patterns, analyzing sources, and using Intrusion Detection Systems. Mitigation strategies include blackhole routing, rate limiting, Web Application Firewall, and Anycast network diffusion. Netizen offers advanced security solutions and…
-

A recent Windows zero-day vulnerability (CVE-2024-38193) was exploited by North Korea’s Lazarus APT group, allowing the installation of the FudModule rootkit. This advanced breach highlights the urgent need for organizations to apply patches promptly and strengthen their security measures to combat increasingly sophisticated cyber threats. Netizen offers advanced security solutions and support services.
-

OpenAI recently shut down an Iranian influence campaign called Storm-2035, using ChatGPT to sway opinions on US political issues and global events. Flint, Michigan suffered a ransomware attack, affecting online services. Amid these challenges, Netizen offers advanced security solutions, compliance support, and automated assessment tools to protect IT infrastructure and mitigate risks.
-

The cybersecurity industry continues to experience rapid growth, driven by the increasing frequency and sophistication of cyber threats. For those looking to start a career in this field, there are numerous entry-level opportunities that offer a solid foundation and promising career trajectory. This guide provides an overview of some common entry-level cybersecurity roles, highlighting key…
-

Large language models like GPT-4 raise concerns as they can autonomously exploit cybersecurity vulnerabilities, posing a significant threat. These AI advancements may enhance defense measures but also empower malicious actors. The cybersecurity community must proactively develop defensive measures and regulate the deployment of these models to mitigate potential risks.