Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Security
-

Windows 11 aims to redefine how anti-malware tools interact with the Windows kernel to enhance system resilience and security following a disruptive IT incident. Meanwhile, the Hadooken malware targets Linux systems with cryptocurrency mining and DDoS attacks, requiring vigilance and mitigation efforts. Netizen offers advanced security solutions, including CISO-as-a-Service, compliance support, and automated vulnerability assessment…
-

Insider threats pose a significant risk to organizations, involving misuse of legitimate access. The Netizen Insider Threat Kill Chain offers a structured approach, highlighting key phases and strategies for effective management. To address common security gaps, a comprehensive approach integrating behavioral analytics, user activity monitoring, and data loss prevention is crucial. Netizen provides advanced solutions,…
-

Windows 11 aims to redefine how anti-malware tools interact with the Windows kernel to enhance system resilience and security following a disruptive IT incident. Meanwhile, the Hadooken malware targets Linux systems with cryptocurrency mining and DDoS attacks, requiring vigilance and mitigation efforts. Netizen offers advanced security solutions, including CISO-as-a-Service, compliance support, and automated vulnerability assessment…
-

Penetration testing, also known as ethical hacking, is essential for evaluating cybersecurity defenses. To prepare effectively for a test, define technical objectives and scope, assemble a response team, obtain authorization, and prepare the environment. Communicate technical details, define reporting and remediation processes, and conduct post-test activities to strengthen security posture. Netizen offers comprehensive cybersecurity services,…
-
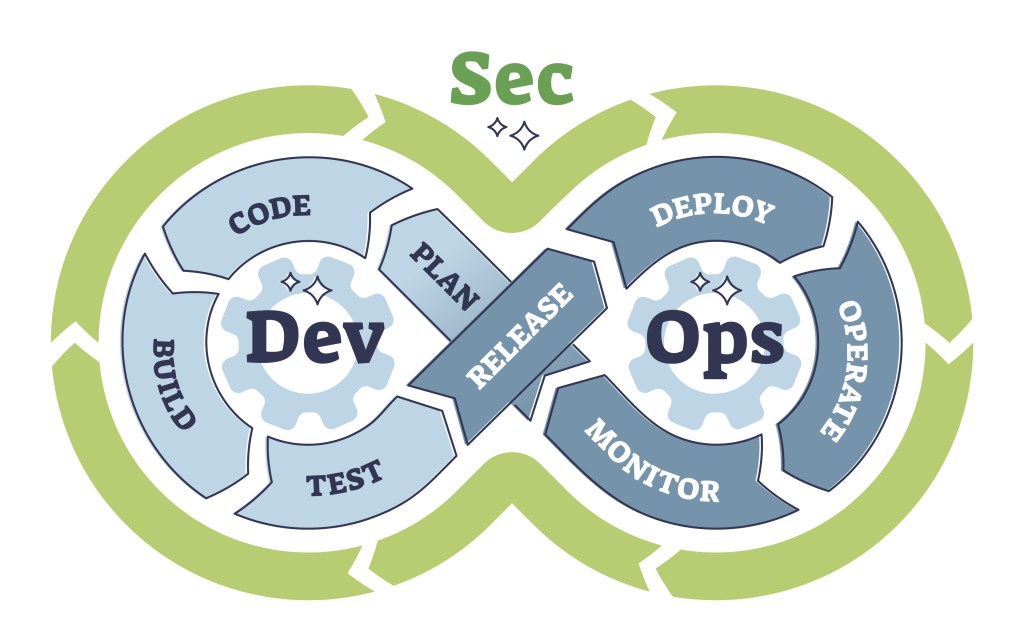
DevOps, DevSecOps, and security posture are essential in modern software development, but often misunderstood. DevOps integrates development and operations to speed up deployment. DevSecOps adds security early in the Agile process and into the containerization and orchestration with automation and thorough documentation. Effective collaboration and cultural change are vital for DevSecOps success.
-

Today’s Topics: CISA Responds to Controversial ‘Airport Security Bypass’ Vulnerability In late August 2024, cybersecurity researchers Ian Carroll and Sam Curry revealed a potentially alarming security flaw within FlyCASS, a third-party web-based application utilized by smaller airlines as part of the Cockpit Access Security System (CASS) and Known Crewmember (KCM) programs. These programs play a…
-

When evaluating ISO 27001 and ISO 27002, it’s essential to understand their distinct roles and purposes in the realm of information security management. Although both standards are closely related, they serve different functions, and recognizing these differences can help you implement them more effectively. General Differences ISO 27001 and ISO 27002 have distinct objectives, which…
-

The National Institute of Standards and Technology (NIST) has recently unveiled three new Federal Information Processing Standards (FIPS) aimed at addressing the emerging challenges posed by quantum computing. These standards—FIPS 203, 204, and 205—represent a pivotal advancement in strengthening the resilience of digital communications against future quantum threats, while also bolstering current cryptographic practices. Overview…
-
Volt Typhoon, a Chinese state-sponsored hacking group, has emerged as a significant player in global cybersecurity, focusing particularly on critical infrastructure. This detailed analysis explores Volt Typhoon’s operations, the impacts of its activities, and how we can effectively defend against such threats. Understanding these aspects is crucial for protecting national security and maintaining global stability.…
-

Security vulnerabilities are a significant concern for businesses. Netizen’s Security Operations Center (SOC) has identified five critical vulnerabilities in popular software and platforms, emphasizing the importance of prompt patching. These vulnerabilities enable remote attackers to execute arbitrary code, manipulate critical data, and disrupt system availability. Netizen offers advanced security solutions to protect businesses from such…