Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
- Instructure Confirms Canvas Data Exposure After ShinyHunters Claims Breach
- What Security Teams Are Seeing in AI-Generated Code
- VECT Ransomware Shows How New RaaS Operations Are Trying to Scale
- Netizen: Monday Security Brief (5/4/2026)
- SIEM Requirements for CMMC 2.0: What Federal Contractors Need to Implement
about
Category: Business
-

The cybersecurity supply chain risk management (C-SCRM) framework plays a pivotal role in ensuring that contractors within the Defense Industrial Base (DIB) are effectively addressing the risks posed by their interconnected supply chains. As noted in the National Institute of Standards and Technology’s (NIST) SP 800-161r1, C-SCRM ensures that organizations can identify, assess, and mitigate…
-
The transition to Cybersecurity Maturity Model Certification (CMMC) 2.0 simplifies compliance for the Defense Industrial Base while aligning with Zero Trust Architecture principles. It consolidates maturity levels, emphasizes identity management, and allows self-assessments for SMBs. Adopting Zero Trust is complex but vital for resilience and meeting stringent cybersecurity requirements.
-

The DoD’s CMMC 2.0, effective December 16, 2024, aims to enhance cybersecurity in the defense supply chain. The model simplifies requirements for SMBs by reducing maturity levels to three, emphasizing self-assessments, and offering phased implementation. Compliance is essential for contract eligibility, providing both challenges and opportunities for SMBs to strengthen cybersecurity practices.
-

Hackers are increasingly targeting supply chains, exploiting vulnerabilities in third-party systems to breach larger networks. Recent high-profile attacks leveraged flaws in common IT tools, causing significant disruptions. To mitigate risks, organizations must implement advanced supplier risk management, secure software pipelines, keep systems updated, and strengthen access controls, among other strategies.
-

The National Institute of Standards and Technology (NIST) has recently unveiled three new Federal Information Processing Standards (FIPS) aimed at addressing the emerging challenges posed by quantum computing. These standards—FIPS 203, 204, and 205—represent a pivotal advancement in strengthening the resilience of digital communications against future quantum threats, while also bolstering current cryptographic practices. Overview…
-
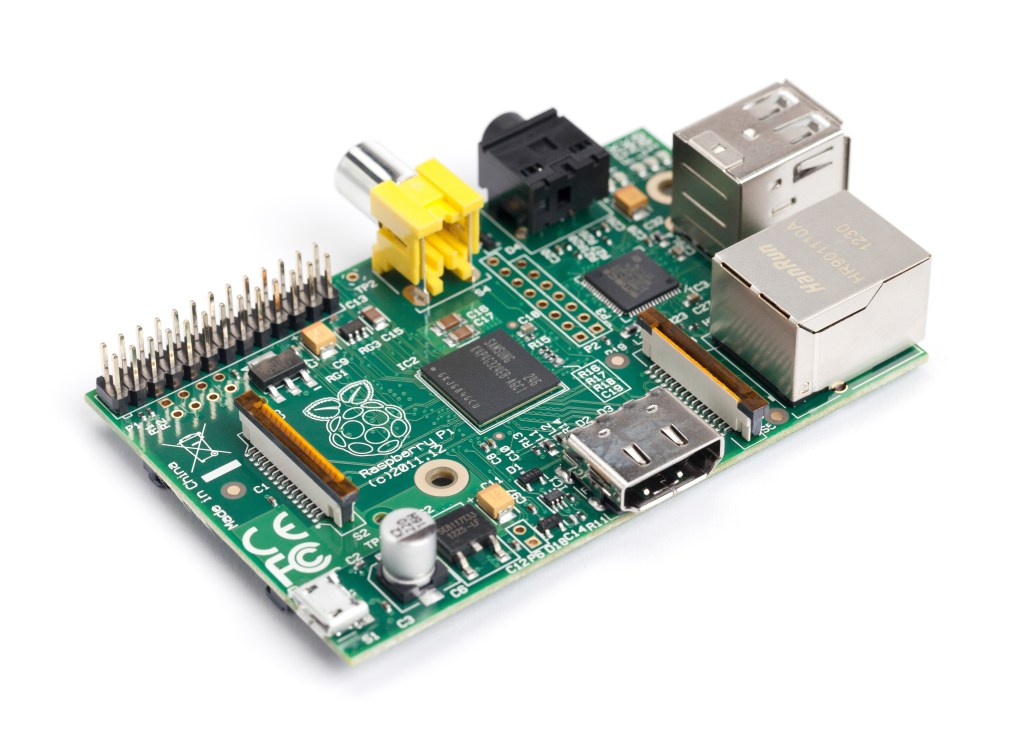
Penetration testing is a flexible skill for cybersecurity analysts. A drop box, like the one built with a Raspberry Pi 3 and TP-Link AC1300 Wi-Fi adapter, provides secure, cost-effective, and easy network access. Netizen offers cybersecurity services, including penetration testing, vulnerability assessments, and automation tools. Visit www.netizen.net/contact for inquiries.
-

The cybersecurity industry continues to experience rapid growth, driven by the increasing frequency and sophistication of cyber threats. For those looking to start a career in this field, there are numerous entry-level opportunities that offer a solid foundation and promising career trajectory. This guide provides an overview of some common entry-level cybersecurity roles, highlighting key…
-

A federal court ruled that a company can be held liable for a data breach at its law firm, permitting a negligence claim against Mondelez Global LLC. This underscores the importance of thorough third-party risk management and data security measures, including evaluations, data minimization, contractual safeguards, continuous monitoring, and robust incident response.
-

Google will no longer trust new TLS server authentication certificates from Entrust and AffirmTrust starting November 1, 2024, due to reported compliance failures and security issues. Website owners are advised to transition to a new Certification Authority to avoid disruptions. Chrome users visiting sites with these certificates will encounter security warnings.
-

Identity and Access Management (IAM) is crucial for controlling access to sensitive information, ensuring security, compliance, and efficiency. It centralizes user identities and access rights, streamlining their management and enforcing precise access controls. IAM verifies user identities, manages access, supports productivity, reduces data breach risks, and simplifies compliance with regulations.