
Overview
- Phish Tale of the Week
- New cybersecurity hirings in the new administration.
- Looking for cybersecurity experts? Consider hiring veterans.
- How Can Netizen Help?
Phish Tale of the Week
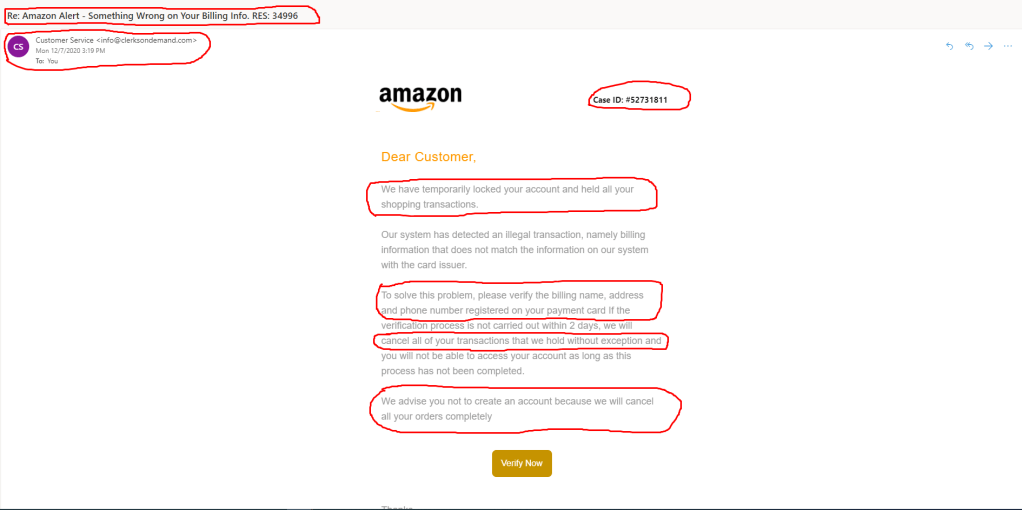
Phishing attempts can often target specific groups that can be exploited by malicious actors. In this instance, we see a phishing scam targeting business/work emails offering an “invoice” as their way in. At first glance, this email masquerades as an everyday dealing in the business world, with either a client or business sending an invoice to your inbox. Unfortunately, this invoice is not as it may seem to be and should not be clicked on.
Take a look below for our reasons why:

- The first red flag on this email is the sender address. Always be hyper-vigilant when receiving emails from an unknown sender. A way to run this email through a quick authenticity check is by googling the sender address after the @.
- The second warning sign in this email is the email title. The title is meant to disguise a malicious link, as an invoice that you may have been expecting from a different company. Always be sure to preview any documents before opening them on your computer.
- The final warning sign for this email is the email thread itself. Most of the time, businesses will attach invoices or documents to previous email chains. The fact that this email isn’t attached to any, and really only just serves as a vessel to deliver an invoice is concerning. Remember, if something looks suspicious, report it to your IT admin or managed service provider for help.
General Recommendations:
A phishing email will typically direct the user to click on a link where they will then be prompted to update personal information, such as a password, credit card, social security, or bank account information. A legitimate company already has this sensitive information and would not ask for it again, especially via email.
- Scrutinize your emails before clicking anything. Have you ordered anything recently? Does this order number match the one I already have? Did the email come from a store you don’t usually order supplies from or a service you don’t use? If so, it’s probably a phishing attempt.
- Verify that the sender is actually from the company sending the message.
- Did you receive a message or email from someone you don’t recognize? Are they asking you to sign into a website to give Personally Identifiable Information (PII) such as credit card numbers, social security number, etc. A legitimate company will never ask for PII via instant message or email.
- Do not give out personal or company information over the internet.
- Do not click on unrecognized links or attachments. If you do proceed, verify that the URL is the correct one for the company/service and it has the proper security in place, such as HTTPS.
Many phishing emails pose a sense of urgency or even aggressiveness to prompt a form of intimidation. Any email requesting immediate action should be vetted thoroughly to determine whether or not it is a scam. Also, beware of messages that seek to tempt users into opening an attachment or visiting a link. For example, an attachment titled “Fix your account now” may draw the question “What is wrong with my account?” and prompt you to click a suspicious link.
Cybersecurity Brief
In this week’s Cybersecurity Brief:
A focus on Cybersecurity in the new administration.
In the wake of one of the furthest reaching hacks in U.S history, President Biden has moved cybersecurity to the top of his agenda. Last week the president announced that he plans to create a new cybersecurity task force headed by Jen Easterly. Easterly was a former special assistant to the Obama administration and was senior director for counterterrorism on The National Security Council. Easterly will be taking a step-back from her current role as head of resilience at Morgan Stanley to lead this newly-created team. Her hiring comes days after multiple news outlets reported that the worst of the Solar-Winds hack has still yet to be uncovered.
What does this mean?
This new agency will focus on improving the United States’ cybersecurity response and readiness. Experts believe that attacks like Solar-Winds may occur more frequent now that the world has seen our response to the most recent attack. “The United States remains woefully unprepared for 21st century security threats – the establishment and prioritization of a DNSA for Cyber and Emerging Tech on the NSC indicates the seriousness the Biden Administration will afford to addressing these challenges,” said Phil Reiner, chief executive of the Institute for Security and Technology. This quote by Reiner reaffirms just how necessary more cybersecurity spending is to focus on new and existing threats The United States currently faces.
In addition, Biden plans to nominate Rob Silvers to replace out-going Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency head Chris Krebs. Silvers previously served as Assistant Secretary for Cyber Policy at the U.S. Department of Homeland Security where he focused on the development and implementation of new Cybersecurity strategies.
Rounding out the new hires is Anne Neuberger as Deputy National Security Adviser for cyber and emerging technology. This position was created to reaffirm the new administrations commitment to protecting our country and it’s businesses online. Neuberger comes from the National Security Agency where she has been lauded the past few years with exposing new hacking-methods from foreign nations to better understand how to prevent and combat them.
To read more about the new hirings, click here.
Looking for cybersecurity experts? Consider hiring veterans
Recently, jobs in cybersecurity have been in very high demand. In The United States alone there are over 1,000,000 openings across a vast array of companies. According to the latest Cybersecurity Workforce Study, The United States needs to increase the number of cybersecurity professionals by 145% to fill the openings currently in the workforce. The U.S Government Accountability office has proposed that companies should increase their internal efforts towards hiring veterans for these positions.
Why Veterans?
With over 200,000 members of the U.S military transitioning from active-duty to civilian life every year, U.S military members are one of the leading sources for new talent in the workforce. These men and women are well-versed in defensive tactics and are accustomed to continuous training that make them excellent candidates for most companies. Veterans are also trusted with advanced computer systems and technology while actively serving regularly. They understand that security is a priority in every company and can apply much of their military training and work ethic to help better secure businesses. While some employees may not see suspicious emails or external storage devices as potential threats, members of the military are constantly on the lookout for ways foreign actors can compromise systems.
How best to help?
Veterans possess many soft-skills such as problem-solving, critical thinking, and analytical skills that help make them ideal candidates. These soft-skills help tremendously in the onboarding and training process that many companies have new employees undergo. Many of these veterans have utilized computer systems when they were in the military and have plenty of skills employers are looking for. All employers need to do is look past their years of experience that can sometimes get lost in translation easily and look towards what kind of an employee they will be for their company. Will they show up on time, be accountable, and be trainable? If the answer is yes, then employers should start looking towards veterans to help fill the need in the cybersecurity workforce.
Find more about this article here.
How Can Netizen Help?
Netizen ensures that security gets built-in and not bolted-on. Providing advanced solutions to protect critical IT infrastructure such as the popular “CISO-as-a-Service” wherein companies can leverage the expertise of executive-level cybersecurity professionals without having to bear the cost of employing them full time.
We also offer compliance support, vulnerability assessments, penetration testing, and more security-related services for businesses of any size and type.
Additionally, Netizen offers an automated and affordable assessment tool that continuously scans systems, websites, applications, and networks to uncover issues. Vulnerability data is then securely analyzed and presented through an easy-to-interpret dashboard to yield actionable risk and compliance information for audiences ranging from IT professionals to executive managers.
Netizen is an ISO 27001:2013 (Information Security Management) certified company. We are a proud Service-Disabled Veteran-Owned Small Business that is recognized by the U.S. Department of Labor for hiring and retention of military veterans.
Calling all top-tier performers looking to drive innovation forward. We favor a “can do” attitude, dedication to continuous learning, commitment to teamwork, and keen attention-to-detail.
Netizen, a national Inc. Magazine Best Workplace and HIRE Vets Platinum Medallion awardee, offers competitive pay and benefits plus ample flexibility, performance incentives, training, and career growth. Equal Opportunity Employer. Military Veterans/Family/Spouses welcome. We are constantly looking for the top industry talent to join our growing team.
Take a look at some of our openings here.


















You must be logged in to post a comment.