
Overview
- Phish Tale of the Week
- IoT Cybersecurity Improvement ACT Passed
- Universities Across The Globe Attacked by Phishing Scam
- How Can Netizen Help?
Phish Tale of the Week
Phishing attempts can often target specific groups that can be exploited by malicious actors. In this instance, we see a phishing scam targeting unsuspecting Amazon customers. This email appears to be a security notification about “illegal transactions” that were made on your Amazon account and require immediate attention. This email contains Amazon’s logo as well a link to fix this issue right in the email, so why not click “verify now”. Unfortunately, there’s plenty or reasons not to click that email right away.
Take a look below:
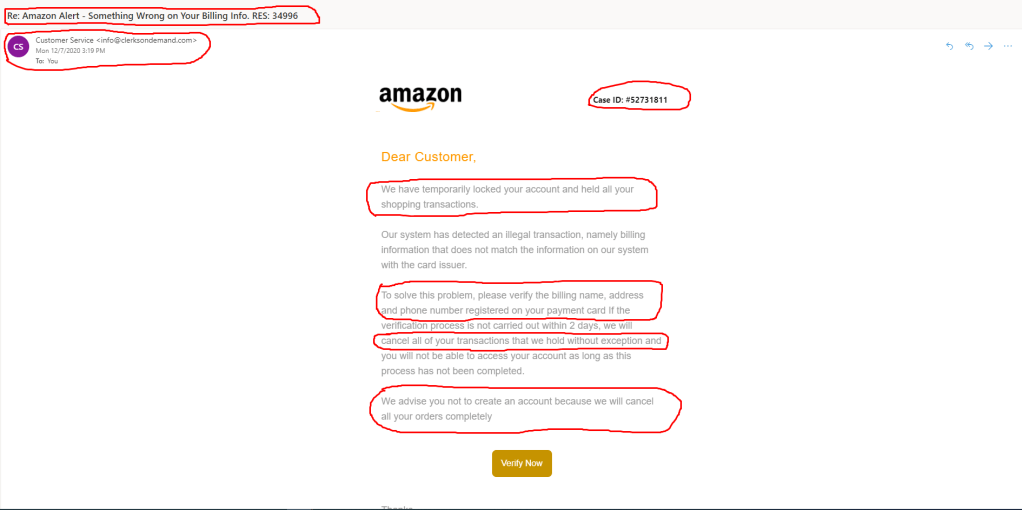
- The first red flag on this email is the sender address. Big corporations like Amazon will never email you outside of their company emails. Seeing that this email was from info@clersondemand.com and not a .amazon.com domain, its safe to say this might be a scam.
- The second warning sign in this email is the email title. The title is meant to create a sense of distress/urgency while also providing a fake invoice number to try to create legitimacy.
- The final warning sign for this email is what is being asked in the email. This sender is requesting us to send back our name, address, and phone number registered on our credit card. Amazon would normally have all of this information already on file, so this raises suspicions immediately. Remember, never give out any of your personal information to random links on the internet.
For Amazon specific recommendations find more here.
General Recommendations:
A phishing email will typically direct the user to click on a link where they will then be prompted to update personal information, such as a password, credit card, social security, or bank account information. A legitimate company already has this sensitive information and would not ask for it again, especially via email.
- Scrutinize your emails before clicking anything. Have you ordered anything recently? Does this order number match the one I already have? Did the email come from a store you don’t usually order supplies from or a service you don’t use? If so, it’s probably a phishing attempt.
- Verify that the sender is actually from the company sending the message.
- Did you receive a message or email from someone you don’t recognize? Are they asking you to sign into a website to give Personally Identifiable Information (PII) such as credit card numbers, social security number, etc. A legitimate company will never ask for PII via instant message or email.
- Do not give out personal or company information over the internet.
- Do not click on unrecognized links or attachments. If you do proceed, verify that the URL is the correct one for the company/service and it has the proper security in place, such as HTTPS.
Many phishing emails pose a sense of urgency or even aggressiveness to prompt a form of intimidation. Any email requesting immediate action should be vetted thoroughly to determine whether or not it is a scam. Also, beware of messages that seek to tempt users into opening an attachment or visiting a link. For example, an attachment titled “Fix your account now” may draw the question “What is wrong with my account?” and prompt you to click a suspicious link.
Cybersecurity Brief
In this week’s Cybersecurity Brief:
Senate Passes Internet of Things Cybersecurity Improvement Act of 2020.
The U.S. senate unanimously passed the Internet of Things (IoT) Cybersecurity Improvement Act of 2020 without any amendments recently. Experts in cybersecurity are lauding the work of Will Hurd (R-Texas) and Robin Kelly (D-Ill) on this bill, calling it some of the most groundbreaking security law in decades. This bipartisan effort would require the federal procurement for and use of IoT devices to adhere to basic security requirements that NIST will be developing. This bill faced no opposition in either the house of representatives or the senate and is now headed to the President’s desk to be signed into law.
What does this mean?
This new act will create a basic set of security standards and practices for all IoT devices used or purchased by the federal government and its industrial base (vendors). One of the first caveats in the bill is that NIST will develop and issue a set of standards-based guidelines for the minimum security that IoT devices owned or used by the federal government and contractors must adhere to. Additionally, The Office of Management and Budget (OMB) must also construct requirements for commercial vendors that perform contract work involving IoT devices to meet information-security policies that are in line with these NIST guidelines. These contractors, IoT vendors, and federal agencies are also going to be required to create and implement a vulnerability-disclosure policy for IoT devices to assist in the reporting of bugs, vulnerabilities, or defects that may be uncovered.
This new act could have significant impacts on IoT resellers and manufacturers, but also has the added benefit of ensuring the security of internet-connected “smart” devices operating on federal government networks which are becoming more and more pervasive. These devices collect and parse data that could be considered highly sensitive, such as video, audio, and other. Developing a standard for IoT security will ensure that a common baseline can be leveraged by both industry and the federal government to ensure vulnerabilities and other threats (like intentional backdoors) are identified and dealt with promptly. . Netizen specializes in the validation, engineering, assessment, and authorization of classified and unclassified systems and devices in accordance with the NIST Risk Management Framework (RMF). We also offer an experienced team of cybersecurity professionals ready to help with any cyber or compliance issue that may arise.
To read more about the IoT Act, click here.
Phishing Campaign Targets Universities
Recently, a string of large-scale phishing attacks were carried out by an organization known as the “Shadow Academy” against some of the world’s most prominent universities. Victims of this attack include the University of Louisiana, University of Washington, University of Arizona, and Oxford University to name a few. Experts believe these attacks were planned to align with the back-to-school chaos that comes from students returning to campus at the start of this most recent fall semester.
How did this happen?
The beginning of the semester is always a busy time for most college students and employees. Work begins to pile up, schedules become full, and the last thing on everyone’s mind is checking which emails are from legitimate sources or not. This, coupled with a large amount of coursework being shifted online instead of in-person, has created a perfect storm for phishing campaigns. The “Shadow Academy” leveraged a technique called domain shadowing to construct harmful landing pages to harvest login credentials across numerous platforms. Some of these malicious domains near perfectly resembled your everyday email you see from popular services such as Facebook, Amazon, and Netflix. In addition to these traps, the “Shadow Academy” also created fake “phishing” emails that appeared to be from a target school’s financial aid department or library in an attempt to trick students and faculty into giving up their information.
What can be done to prevent this?
Netizen specializes in cybersecurity solutions including penetration testing, vulnerability assessments, advisory, and 24×7 monitoring. In addition to these services, we also offer social engineering and phishing campaigns in attempt to better prepare individuals with what to watch out for when they are using the internet. Netizen’s experienced team of cybersecurity professionals stands ready to help with any cyber or compliance issue that may arise, leveraging advanced tools, such as the award-winning Overwatch suite, and intelligent automation. A cost-effective cybersecurity monitoring program coupled with social engineering testing and employee training would help prevent such attacks by educating your staff on how to identify, handle, and report suspicious behavior.
Find more about this article here.
How Can Netizen Help?
Netizen ensures that security gets built-in and not bolted-on. Providing advanced solutions to protect critical IT infrastructure such as the popular “CISO-as-a-Service” wherein companies can leverage the expertise of executive-level cybersecurity professionals without having to bear the cost of employing them full time.
We also offer compliance support, vulnerability assessments, penetration testing, and more security-related services for businesses of any size and type.
Additionally, Netizen offers an automated and affordable assessment tool that continuously scans systems, websites, applications, and networks to uncover issues. Vulnerability data is then securely analyzed and presented through an easy-to-interpret dashboard to yield actionable risk and compliance information for audiences ranging from IT professionals to executive managers.
Netizen is an ISO 27001:2013 (Information Security Management) certified company. We are a proud Service-Disabled Veteran-Owned Small Business that is recognized by the U.S. Department of Labor for hiring and retention of military veterans.


Leave a comment