Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Threat Intelligence
-

CISA identified the CVE-2021-26829 vulnerability in OpenPLC ScadaBR as actively exploited, linking it to attacks by the pro-Russian group TwoNet. North Korean operators have also uploaded malicious npm packages, continuing their Contagious Interview campaign. Netizen offers advanced cybersecurity services, positioning itself as a trusted partner for sensitive organizations.
-

CISA has mandated federal agencies to address a critical VMware Tools vulnerability exploited by Chinese state hackers. Additionally, a report has uncovered a YouTube campaign that used over 3,000 malware-laden videos to disseminate credential-stealing software.
-

ChatGPT’s Atlas browser combines browsing with an LLM, increasing security risks via prompt injection vulnerabilities. It blurs boundaries between browsing functions and language processing, exposing users to potential operational threats. Enhanced control measures are crucial for organizations adopting agent-based systems, necessitating least-access permissions, sandbox execution, and rigorous authentication processes.
-
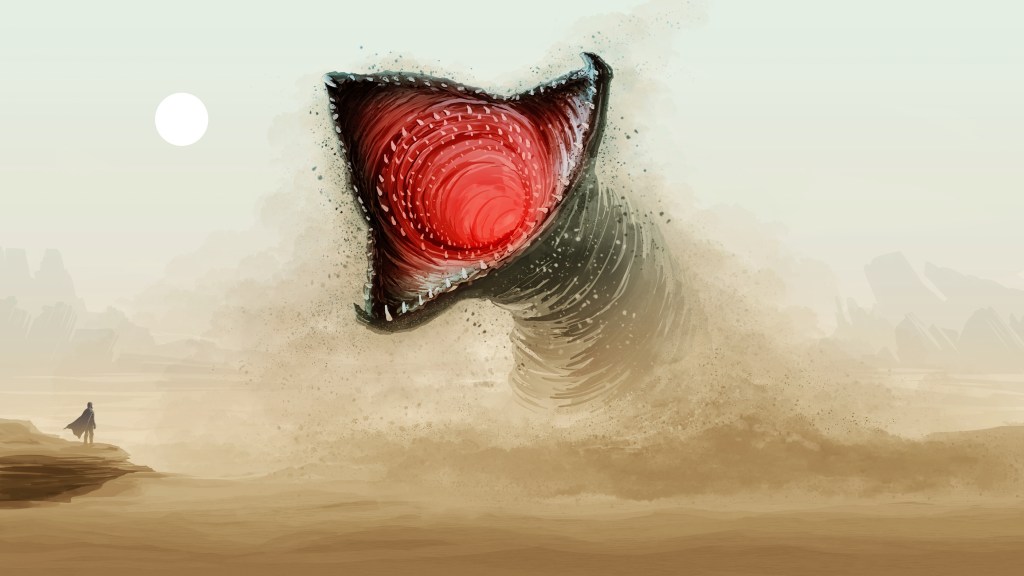
A surge of malicious activity in the npm ecosystem re-emerged on November 24, linked to the Shai Hulud campaign. The attack targets gaps in authentication token migration, potentially compromising developer environments. Hundreds of packages were affected, prompting organizations to audit dependencies, rotate credentials, and enhance security measures to mitigate risks associated with exposed secrets.
-

Recent cyber threats include a flaw in 7-Zip’s symbolic link processing, tracked as CVE-2025-11001, and a Salesforce supply-chain breach involving Gainsight, which allowed OAuth token theft. Organizations are encouraged to update software and establish clear access policies for third-party integrations to mitigate risks and enhance cybersecurity. Netizen offers solutions for secure IT infrastructure.
-

In September 2025, AI-driven cyber espionage was revealed as a significant global threat, with a Chinese group autonomously infiltrating organizations using Anthropic’s Claude Code model. Concurrently, Amazon identified attacks exploiting zero-day vulnerabilities in Cisco and Citrix systems, emphasizing the need for enhanced network security and monitoring against advanced threats in identity infrastructures.
-

Security Operations Centers (SOCs) traditionally relied on static indicators of compromise, which have become ineffective against rapidly evolving threats. Transitioning to intent-based detection allows SOCs to focus on an attacker’s objectives rather than specific tools, enhancing threat detection and response. This shift involves adopting behavioral analytics and improving collaboration with threat intelligence teams.
-

A new wave of phishing attacks, utilizing ClickFix pages and PureRAT malware, targets hotel booking accounts, compromising systems and stealing credentials. Microsoft warns about Whisper Leak, a privacy threat that exposes AI chatbot conversation topics despite encryption. Businesses are urged to bolster cybersecurity and assess their defenses against these threats.
-

Patch management is crucial for cybersecurity, yet organizations often face patch lag due to conflicting IT goals and legacy systems. Delays can lead to significant vulnerabilities and compliance issues, while attackers exploit known flaws quickly. Continuous patching and risk-based approaches are necessary. Netizen offers proactive services to enhance patch management and security effectiveness.
-

The expiration of the Cybersecurity Information Sharing Act (CISA) disrupts the legal framework for threat intelligence sharing, leading organizations to reevaluate their collaboration strategies. Without CISA’s protections, companies face new privacy and liability challenges, prompting a shift toward privacy engineering, enhanced vendor scrutiny, and a need for stronger governance to maintain effective information exchange.