Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Security
-

This content covers phishing tactics targeting Amazon users, EU scrutiny of Meta, and a federal recovery from a CrowdStrike outage. It advises caution with unsolicited links and attachments, scrutinizing messages, and not divulging personal information online. It also highlights Netizen’s cybersecurity solutions including CISO-as-a-Service and vulnerability assessments.
-

Netizen’s Security Operations Center (SOC) has identified five critical vulnerabilities from July that require immediate patching or remediation. These include high-severity issues in Microsoft’s Windows Hyper-V, SharePoint, Rejetto HTTP File Server, Azure Kinect SDK, and OpenSSH. Netizen provides advanced security solutions and services, including compliance support, vulnerability assessments, and automated assessment tools.
-
A Spanish-speaking cybercrime group named GXC Team has been observed elevating the standard of phishing attacks by bundling phishing kits with malicious Android applications. This innovative approach has taken malware-as-a-service (MaaS) offerings to the next level. Singaporean cybersecurity firm Group-IB has been tracking this e-crime actor since January 2023, describing their solution as a “sophisticated…
-

The Federal Bureau of Investigation (FBI) has announced the successful execution of Operation Endgame, a groundbreaking multinational cyber operation aimed at dismantling a sophisticated network of cybercriminals. This unprecedented initiative involved coordinated efforts from law enforcement agencies across the United States, Denmark, France, Germany, the Netherlands, the United Kingdom, and other countries, with crucial support…
-
In recent developments, a significant vulnerability has been identified in ARM’s Memory Tagging Extension (MTE), a security feature designed to mitigate memory corruption issues in the ARMv8.5-A architecture. This vulnerability exploits speculative execution, a performance optimization feature in modern CPUs, to bypass MTE’s protections and leak sensitive information. Understanding Memory Tagging Execution (MTE) MTE aims…
-

In June 2024, CDK Global, a crucial software provider for auto dealerships, experienced a severe cyberattack by the ransomware group BlackSuit. The attack began on June 19 and led to the shutdown of CDK’s systems until July 5, significantly impacting dealership operations across North America. This incident left approximately half of the nation’s car dealerships…
-

Atlassian has released crucial security updates for its Bamboo, Confluence, and Jira products, addressing high-severity vulnerabilities. These updates fix issues such as server-side request forgery (SSRF) and file inclusion vulnerabilities, as well as denial-of-service (DoS) flaws. Users are advised to apply these patches promptly to prevent unauthorized access and service disruptions.
-

On July 19, 2024, a routine software update by CrowdStrike caused widespread disruptions in multiple industries, leading to system crashes and operational challenges for airlines, emergency services, and financial institutions. The incident revealed the risks of overreliance on a single security vendor and highlighted the need for diversification and comprehensive security strategies. Netizen offers advanced…
-

A federal court ruled that a company can be held liable for a data breach at its law firm, permitting a negligence claim against Mondelez Global LLC. This underscores the importance of thorough third-party risk management and data security measures, including evaluations, data minimization, contractual safeguards, continuous monitoring, and robust incident response.
-
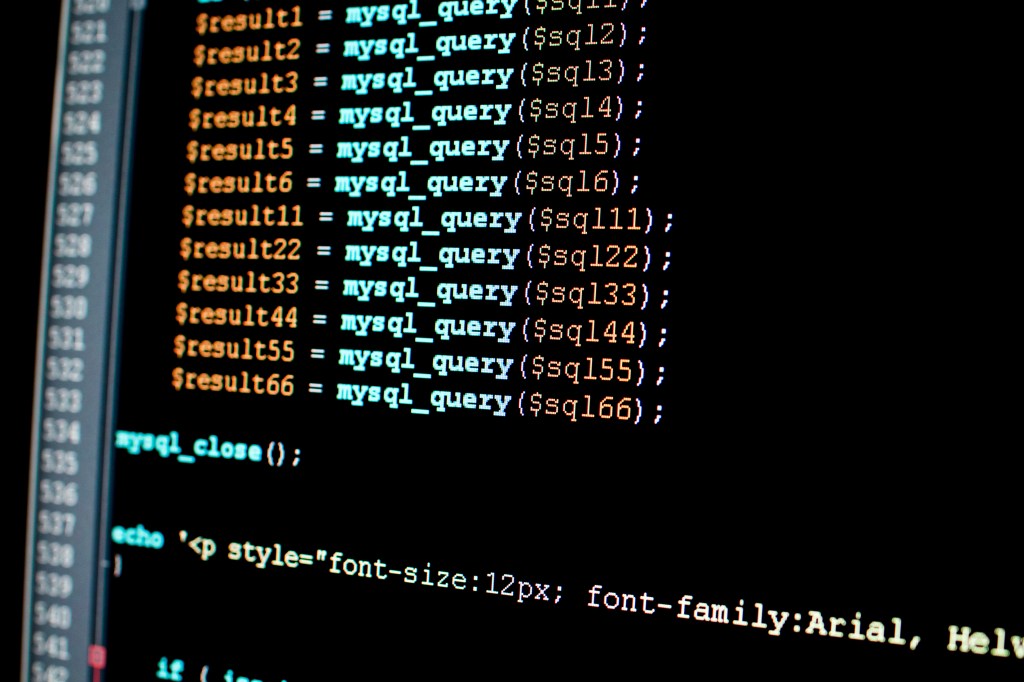
Ivanti has addressed high-severity vulnerabilities in its Endpoint Manager (EPM) and Endpoint Manager for Mobile (EPMM) products. The most critical is an SQL injection flaw (CVE-2024-37381) affecting the Core server of EPM 2024 flat, allowing authenticated attackers with network access to execute arbitrary code. Hotfixes and updates are available for mitigation.