
Overview
- Phish Tale of the Week
- First American Financial Corp. Leaks 800+ Million Records
- Google Begins Tracking “zero-day” Exploits
- How Can Netizen Help?
Phish Tale of the Week
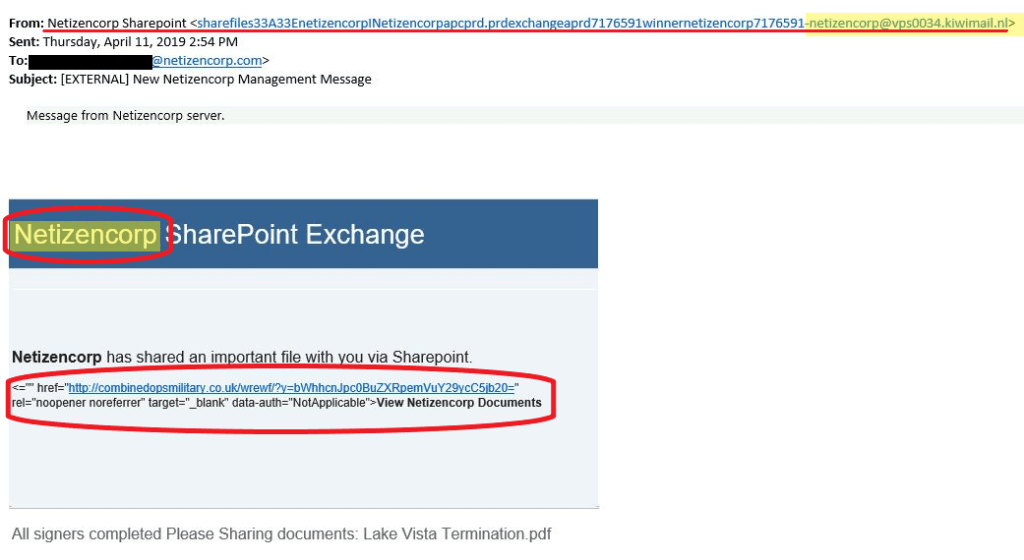
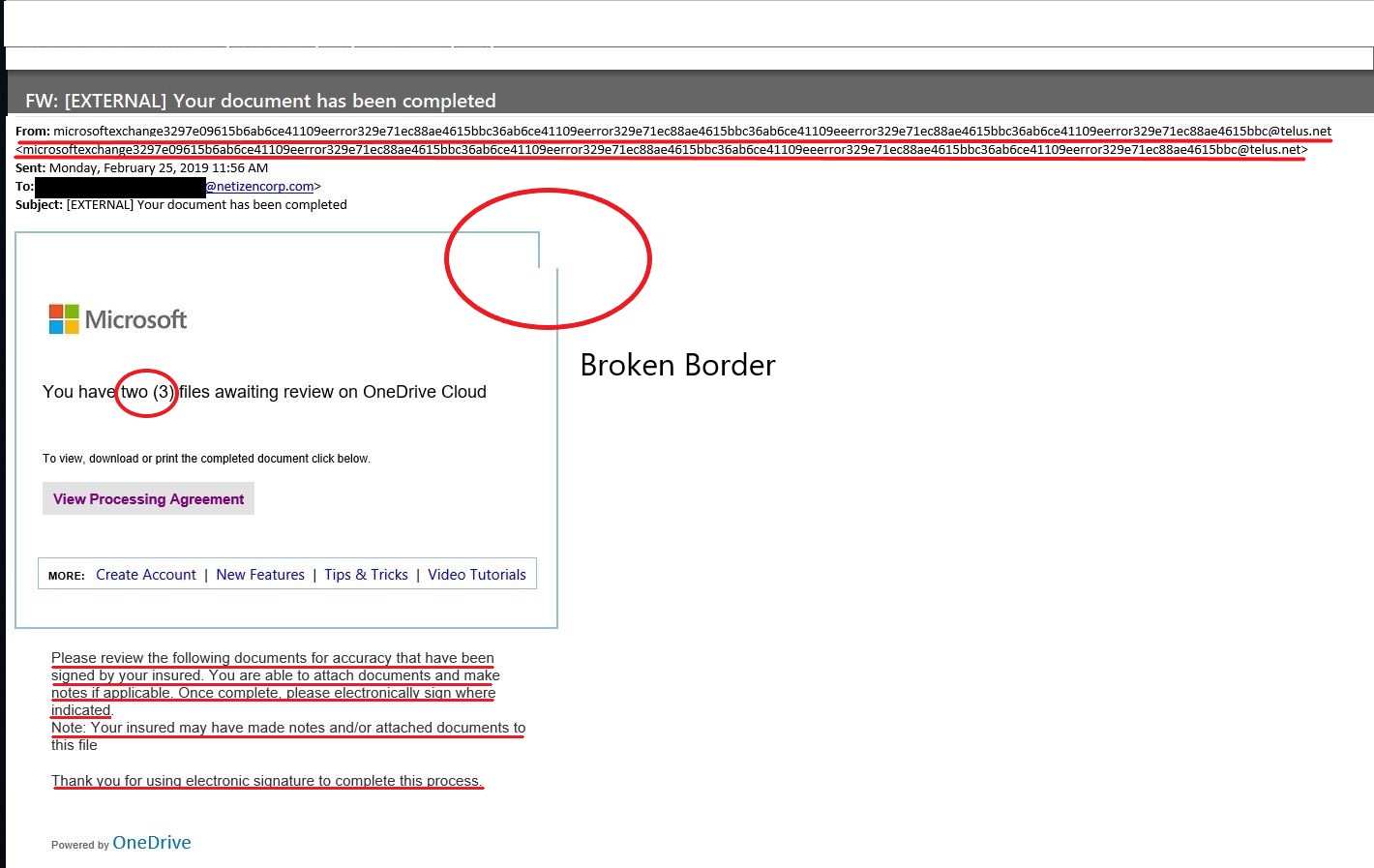
One way a malicious actor can try to collect a business’ sensitive information is by targeting the business’ employees. Attempting to phish an employee requires some research about the company and the potential victim. The following is a phishing attempt that was received in our office last week.
This particular phishing attempt is almost unidentifiable because of the degree of attention that must be paid to pick out the telling factors. The email addresses the recipient by name, indicating that there was some research done to find the individual’s full name and email address. This process is called “social engineering” and is used to collect a victim’s information.
Take a look below:

- Some tell-tale signs that raise suspicions:The first sign of an email received from outside of the Netizen environment is the “EXTERNAL” tag in the email subject line.
- The email contains a typo where the recipient is encouraged to call for questions, but a phone number was never provided.
- An unusually long site address from “AWStrackme” appears at the bottom of the email.
General Recommendations:
A phishing email will typically direct the user to visit a website where they are asked to update personal information, such as a password, credit card, social security, or bank account numbers. A legitimate company already has this sensitive information and would not ask for it again, especially via email.
- Scrutinize your emails before clicking anything. Did you order or ask for anything for which you’re expecting a confirmation? Did the email come from a store you don’t usually order supplies from or a service you don’t use? If so, it’s probably a phishing attempt.
- Verify that the sender is actually from the company sending the message.
- Did you receive a message or email from someone you don’t recognize? Are they asking you to sign into a website to give Personally Identifiable Information (PII) such as credit card numbers, social security number, etc. A legitimate company will never ask for PII via instant message or email—this is a huge red flag.
- Do not give out personal or company information.
- Review both signature and salutation.
- Do not click on attachments.
- Do not click on unrecognized links. If you do proceed, verify that the URL is the correct one for the company/service and it has the proper security in place, such as HTTPS.
- Be wary of poor spelling, grammar, and formatting. As can be seen with the with this email, there are multiple spelling, grammar, and formatting errors, leading us to believe that the message is illegitimate. If an email is visually unprofessional, the sender is likely not who they say they are.
Many phishing emails pose a sense of urgency or even aggressiveness to prompt a form of intimidation. Any email requesting immediate action or that is addressing you in a threatening manner should be questionable. Also, beware of messages that seek to tempt users into opening an attachment or visiting a link. For example, an attachment titled “Staff Pay Raises 2019” may seem like something you really want to know about, but it could just be a ploy to plant malware on your system or steal your credentials.
Cybersecurity Brief
In this week’s Cybersecurity Brief: First American Financial Corp. Leaked Hundreds of Millions of Insurance Records, Google Begins Tracking “Zero-Day” Vulnerabilities
First American Corp. Title Insurance Records Leak

First American Financial Corp., a Fortune 500 Company, is a national leading provider of title insurance and settlement services to the real estate and mortgage industries with millions of customers. Late last week, it was discovered that First American’s website has a major security flaw that allows anyone with a URL to a document held by the company to access other documents simply by changing a single digit in the URL. The website reportedly has exposed more than 800 million files dating all the way back to 2003. The digital files include many forms of sensitive customer information that could be used by malicious actors, including: bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts, and drivers license images. Many of the exposed files are records of wire transactions with bank account numbers and other information from home or property buyers and sellers.
A spokesman for First American Financial Corp. shared the following statement:
“First American has learned of a design defect in an application that made possible unauthorized access to customer data. At First American, security, privacy and confidentiality are of the highest priority and we are committed to protecting our customers’ information. The company took immediate action to address the situation and shut down external access to the application. We are currently evaluating what effect, if any, this had on the security of customer information. We will have no further comment until our internal review is completed.”
The information released by this security flaw could be a potential gold mine to phishers and scammers looking to cash-in on this data leak. With access to home addresses, bank account numbers and social security information, scammers can try to convince a homeowner to wire funds to a fraudulent account.
For First American Financial Corp. Customers, it is recommended that you:
- Closely monitor the situation and pay attention to the company’s updates.
- Monitor your bank account and credit statements for suspicious activities.
- Do NOT provide any information to calls/emails asking you to wire funds. Contact First American Financial Corp. Customer Service if you receive such calls.
To read more about the First American Financial Corp. leak, click here.
Google Begins Tracking Zero-Day Vulnerabilities

The Google Project Zero team, a group of top Google security researchers with the sole mission of tracking down and neutralizing the most harmful security flaws in the world’s software, has begun documenting zero-day vulnerabilities exploited in the wild. These secret hack-able flaws, known in the security industry as “zero-day” vulnerabilities, are exploited by criminals, state-sponsored hackers and intelligence agencies in their spying operations.
The security research team is compiling a list of these vulnerabilities that had been exposed before the vendor of the software could patch the security flaws. The spreadsheet currently lists over 100 vulnerabilities exploited in the wild since 2014. The table includes the flaw’s CVE identifier, impacted vendor, impacted product, the type of vulnerability, a brief description, the date of its discovery, the date when a patch was released, a link to the official advisory, a link to a resource analyzing the flaw, and information on attribution. The list currently includes vulnerabilities affecting products from Facebook, Microsoft, Google, Apple, Adobe, Mozilla, Cisco, Oracle, IBM and Ghostscript. The data from this research shows that, on average, there is a new exploit identified every 17 days. The data also reveals that it takes vendors roughly 15 days to patch the exploited flaw after it becomes public.
The Big Picture:
No business or organization is invulnerable to a cyberattack, as these incidents prove. Business and safety operations can be heavily impacted and result in the loss of millions of dollars. To better protect your business or organization, take a proactive stance about cybersecurity.
To read the original article by SecurityWeek, click here.
How Can Netizen Help?
Netizen ensures that security gets built-in and not bolted-on. Providing advanced solutions to protect critical IT infrastructure such as the popular “CISO-as-a-Service” wherein companies can leverage the expertise of executive-level cybersecurity professionals without having to bear the cost of employing them full time.
We also offer compliance support, vulnerability assessments, penetration testing, and more security-related services for businesses of any size and type.
Additionally, Netizen offers an automated and affordable assessment tool that continuously scans systems, websites, applications, and networks to uncover issues. Vulnerability data is then securely analyzed and presented through an easy-to-interpret dashboard to yield actionable risk and compliance information for audiences ranging from IT professionals to executive managers.
Netizen is an ISO 27001:2013 (Information Security Management) certified company. We are a proud Service-Disabled Veteran-Owned Small Business that is recognized by the U.S. Department of Labor for hiring and retention of military veterans.



Copyright © 2019 Netizen Corporation. All rights reserved.

 Netizen, which was founded in September 2013, is also one of the fastest growing companies in the Lehigh Valley region of Pennsylvania, where it is headquartered. They have satellite offices in Arlington, VA and Charleston, SC as well as field locations around the country in places like Orlando, FL and Huntsville, AL. Netizen has received several other notable awards recently including the U.S. Department of Labor HIREVets Platinum Medallion, Lehigh Valley Veteran Owned Business of the Year, and Charleston Defense Summit Innovation Spotlight.
Netizen, which was founded in September 2013, is also one of the fastest growing companies in the Lehigh Valley region of Pennsylvania, where it is headquartered. They have satellite offices in Arlington, VA and Charleston, SC as well as field locations around the country in places like Orlando, FL and Huntsville, AL. Netizen has received several other notable awards recently including the U.S. Department of Labor HIREVets Platinum Medallion, Lehigh Valley Veteran Owned Business of the Year, and Charleston Defense Summit Innovation Spotlight.















You must be logged in to post a comment.