
Overview
- Phish Tale of the Week
- Self-Promoting Cybersecurity Firms Doing More Harm Than Good
- Almost 500,000 job openings in cybersecurity nationwide
- How can Netizen help?
Phish Tale of the Week
Phishing attempts can often target specific groups that can be exploited by malicious actors. In this instance, we see a phishing scam targeting unsuspecting FedEx customers. This email appears to be a warning notice that the client’s package was unable to be deliver. This email contains FedEx’s official logo as well a shortcut to fix this issue right in the email, so why not click “update address”. Unfortunately, there’s plenty or reasons not to click that email right away.
Take a look below:
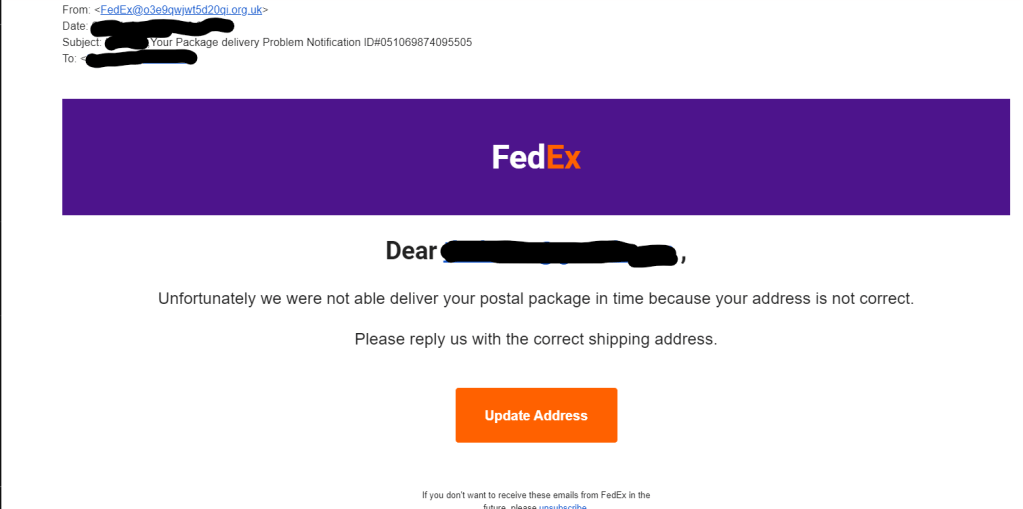
- The first red flag on this email is the sender address. Big corporations like FedEx will never email you outside of their company emails. In the future, check all suspicious emails from companies against previous correspondences you’ve received and make sure the sender address is the same.
- The second warning sign in this email is the email title. The title is meant to create a sense of distress/urgency while also providing a fake support number to try to create legitimacy.
- The final warning sign for this email is the messaging inside the email. In this instance, we are being notified that our that a package was unable to be delivered. We are then given a shortcut to update our address Phishing campaigns like this will almost always try to convince you to click on a link or shortcut to navigate you out of your email browser. Remember, if a link or shortcut looks suspicious, do not click on it.
For more phishing examples from FedEx, check out this link.
General Recommendations:
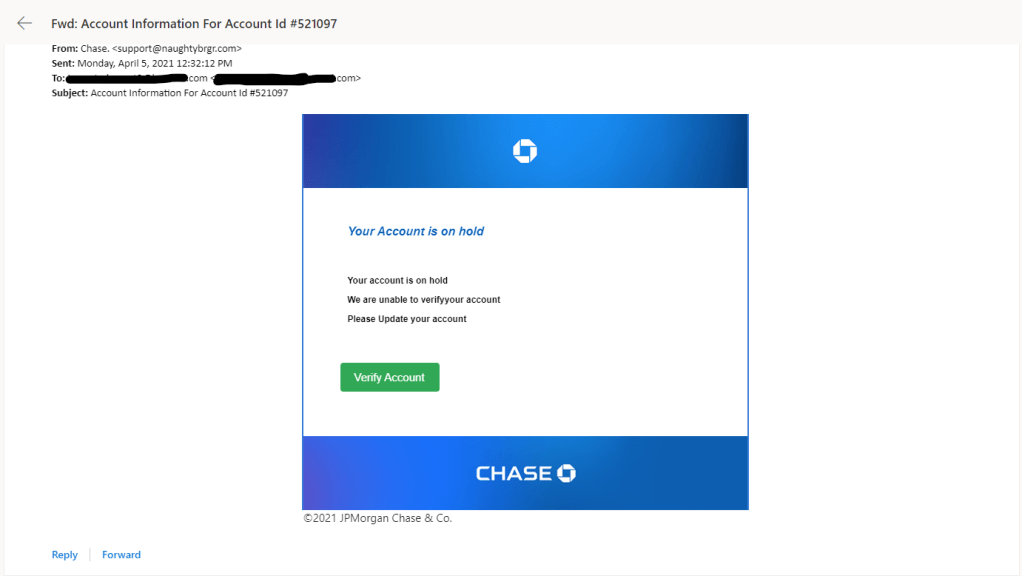
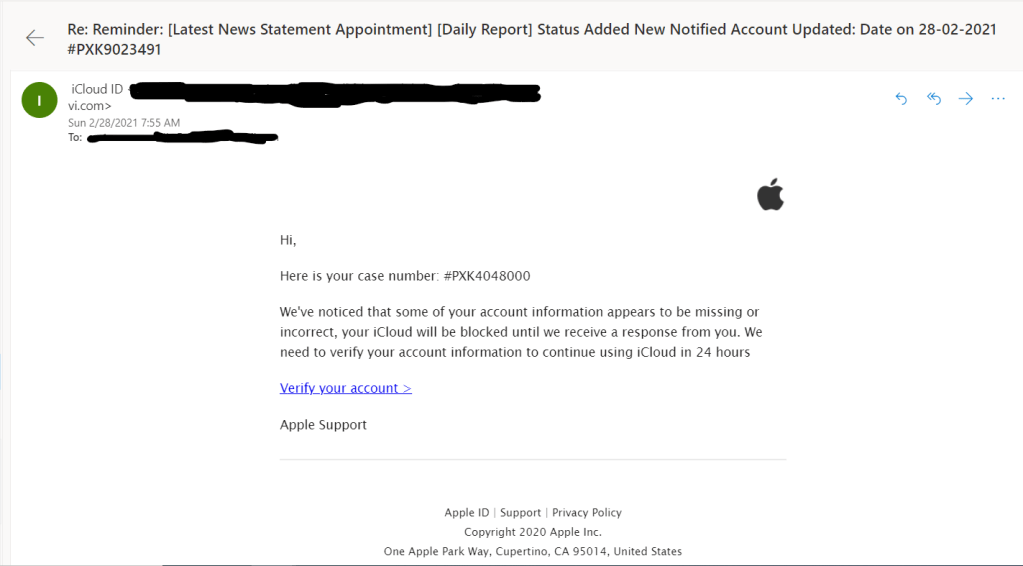
A phishing email will typically direct the user to click on a link where they will then be prompted to update personal information, such as a password, credit card, social security, or bank account information. A legitimate company already has this sensitive information and would not ask for it again, especially via email.
- Scrutinize your emails before clicking anything. Have you ordered anything recently? Does this order number match the one I already have? Did the email come from a store you don’t usually order supplies from or a service you don’t use? If so, it’s probably a phishing attempt.
- Verify that the sender is actually from the company sending the message.
- Did you receive a message or email from someone you don’t recognize? Are they asking you to sign into a website to give Personally Identifiable Information (PII) such as credit card numbers, social security number, etc. A legitimate company will never ask for PII via instant message or email.
- Do not give out personal or company information over the internet.
- Do not click on unrecognized links or attachments. If you do proceed, verify that the URL is the correct one for the company/service and it has the proper security in place, such as HTTPS.
Many phishing emails pose a sense of urgency or even aggressiveness to prompt a form of intimidation. Any email requesting immediate action should be vetted thoroughly to determine whether or not it is a scam. Also, beware of messages that seek to tempt users into opening an attachment or visiting a link. For example, an attachment titled “Fix your account now” may draw the question “What is wrong with my account?” and prompt you to click a suspicious link.
Cybersecurity Brief
In this week’s Cybersecurity Brief:
Self-Promoting Cybersecurity Firms Doing More Harm Than Good

Ransomware attacks are some of the most costly and destructive cyberattacks circulating the world today. They work through a malicious software being downloaded or applied to a target’s systems which then blocks access to information, encrypting the data, and demanding a ransom be paid to free up the systems. This type of attack recently gained national attention when the Colonial Pipeline was forced to pay a $5,000,000 ransom to a cybercriminal group known as DarkSide. In the race to combat these attacks many companies have begun staffing teams of trained cyber professionals to crack the cyphers attached to these attacks. After figuring out a way to bypass the ransom and thwart the hackers, many groups launch massive press releases or blog posts illustrating their victories. What if I told you the companies working around the clock to fight these cybercriminal groups may be doing more harm than good?
Four months before DarkSide gained national attention over their ransomware exploits, antivirus company Bitedefender declared that it was “happy to announce” a major breakthrough. Bitedefender had been working on a solution to DarkSide’s ransomware and after finally making a breakthrough, they announced to the world that they would offer this tool for free to anyone affected by DarkSide’s activities. Unbeknownst to them, another pair had already uncovered this flaw in DarkSide’s ransomware.
Fabian Wosar and Michael Gillespie are two names you probably have not heard of. They are not featured in the news or on television and that is they want it. Both Wosar and Gillespie belong to a group known as the Ransomware Hunting Team, a non-profit, invitation only group focused on combating cybercriminals and helping victims affected by ransomware. In December of 2020, Gillespie looked to team up with Wosar to isolate an encryption key to help speed up the recovery process that comes after paying Darkside’s ransomware bounty. The two gentlemen quickly discovered that their work isolating this one key could be utilized on other files that had been infected by DarkSide. Gillespie later posted a ground-breaking discovery to the rest of the Hunting Team that DarkSide was re-using RSA keys from previous ransomware attacks.
For those unfamiliar, RSA is a public-key cryptosystem that is widely used for secure data transmission. RSA first generates a public key to encode data, then a private key is created to decipher it. RSA is used in many legitimate aspects of ecommerce and communications such as encrypting credit card transactional data and securing VPN connections between clients and servers. Unfortunately, its legitimate uses have been overshadowed by its repurposement as a tool for cybercriminals to help extort more money out of business owners.
In review, was Bitedefender right to publish their findings? On one hand, disclosing this information immediately alerted DarkSide that people had found a loophole to avoid paying the ransom. On the contrary, Bitedefender has a national following and recognition and was probably able to reach a greater number of users than the Ransomware Hunting Team was able to.
To read more about this article, click here.
Almost 500,000 job openings in cybersecurity nationwide

With life returning to some resemblance of normalcy job openings have begun to flood the marketplace. One of the most in-demand industries? Cybersecurity. Cyber Seek, a tech job tracking database from the U.S Commerce department reported that there are over 465,000 open positions in cybersecurity nationwide. For anyone looking to start or pivot to a different career in cybersecurity, the time is now.
Recent increases in cyberattacks have helped spur an increase in demand for cybersecurity professionals. Companies are now more than ever looking to secure their information technology systems from outside threats. Both private businesses and government agencies alike are looking to fill these vacancies in desirable locations such as Florida, Virginia, California, and Texas. Vice President of research at CompTIA, Tim Herbert, had this to add “You don’t have to be a graduate of MIT to work in cybersecurity”. While going to a four-year university and pursing a degree in cybersecurity is one avenue towards a career in cyber, it is not the only one. Cybersecurity hopefuls could look to grab a Security+ or Network+ certification to help increase their marketability as a job candidate. Additionally, many companies offer 6, 8, or 10 week “boot camps” meant to prepare individuals with many of the skills they will need for a career in cyber.
The largest catalyst for this tremendous amount of job openings is a lack of skilled workers. Many individuals see the responsibilities that come with working in cybersecurity and worry that they will not be able to fulfill them. “Cybersecurity is not rocket science, but it’s not like you can just walk in the door and take a job and pick it up like that”, Michelle Moore added, a cybersecurity professor at The University of San Diego. People looking to start a career in cybersecurity have to be willing to put the time and effort into honing this new craft. If they make that commitment, they will be rewarded with jobs helping secure our nations critical infrastructure and combating cybercriminals with many opportunities to take on more responsibilities.
Calling all top-tier performers looking to drive innovation forward. We favor a “can do” attitude, dedication to continuous learning, commitment to teamwork, and keen attention-to-detail. Netizen, a national Inc. Magazine Best Workplace and HIRE Vets Platinum Medallion awardee, offers competitive pay and benefits plus ample flexibility, performance incentives, training, and career growth. Equal Opportunity Employer. Military Veterans/Family/Spouses welcome.
Check out some of our open positions here.
How Can Netizen Help?
Netizen ensures that security gets built-in and not bolted-on. Providing advanced solutions to protect critical IT infrastructure such as the popular “CISO-as-a-Service” wherein companies can leverage the expertise of executive-level cybersecurity professionals without having to bear the cost of employing them full time.
We also offer compliance support, vulnerability assessments, penetration testing, and more security-related services for businesses of any size and type.
Additionally, Netizen offers an automated and affordable assessment tool that continuously scans systems, websites, applications, and networks to uncover issues. Vulnerability data is then securely analyzed and presented through an easy-to-interpret dashboard to yield actionable risk and compliance information for audiences ranging from IT professionals to executive managers.
Netizen is an ISO 27001:2013 (Information Security Management) certified company. We are a proud Service-Disabled Veteran-Owned Small Business that is recognized by the U.S. Department of Labor for hiring and retention of military veterans.






















You must be logged in to post a comment.