
Overview
- Phish Tale of the Week
- Lithuania Suffers a Series of DDOS Attacks Following The Ban of Kaliningrad Imports
- Carnival Cruise Lines Hit With $5,000,000 Fine for Cybersecurity Incidents
- How can Netizen help?
Phish Tale of the Week
Phishing attempts can often target specific groups that can be exploited by malicious actors. In this instance, we see a phishing scam targeting unsuspecting debt holders. This email appears to be a notification alerting us to answer and win a new Makita Power Drill. We are then prompted to “get started now” to complete the survey for the free reward. This email contains a note about receiving a free drill for only a few minutes of our time, so why not click here? Unfortunately, there are plenty of reasons not to click that email right away.
Take a look below:
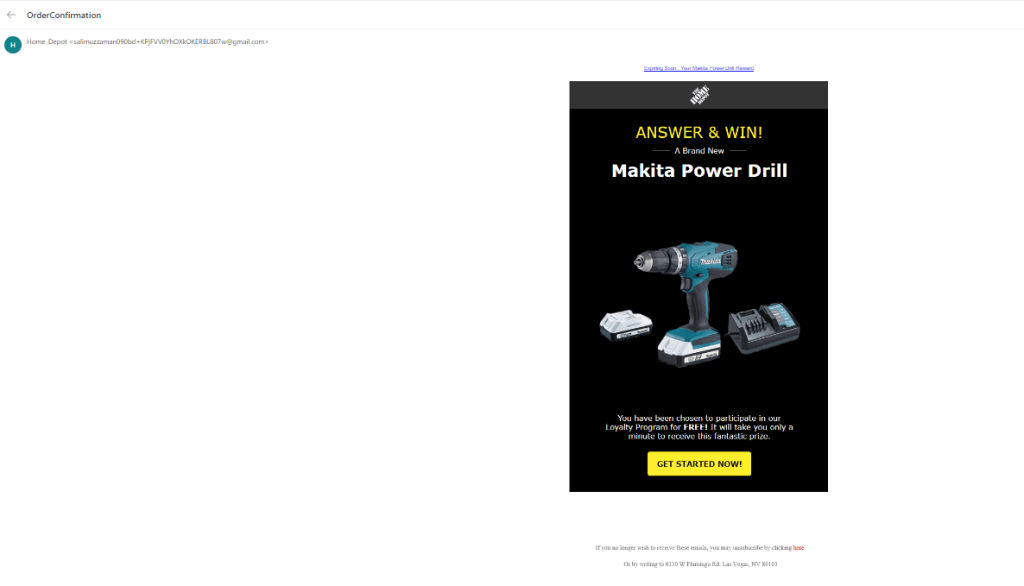
- The first red flag on this email is the sender’s address. Always thoroughly inspect the sender’s address to ensure it’s from a trusted sender. In the future, review the sender’s address thoroughly to see if the email could be coming from a threat actor.
- The second warning sign in this email is the “expiring soon” notice above the main message. Phishing scams commonly use words like this to elicit a quick response from their targets. Always be sure to thoroughly inspect the messaging of all emails in your inbox.
- The final warning sign for this email is the large red “Get Started Now” call to action. Threat actors use call-to-action buttons like this to immediately redirect targets to malicious landing pages. These landing pages then infect the target’s system with malware or other software with the intention of stealing information or further extortion.
General Recommendations:
A phishing email will typically direct the user to click on a link where they will then be prompted to update personal information, such as a password, credit card, social security, or bank account information. A legitimate company already has this sensitive information and would not ask for it again, especially via email.
- Scrutinize your emails before clicking anything. Have you ordered anything recently? Does this order number match the one I already have? Did the email come from a store you don’t usually order supplies from or a service you don’t use? If so, it’s probably a phishing attempt.
- Verify that the sender is actually from the company sending the message.
- Did you receive a message or email from someone you don’t recognize? Are they asking you to sign into a website to give Personally Identifiable Information (PII) such as credit card numbers, social security number, etc. A legitimate company will never ask for PII via instant message or email.
- Do not give out personal or company information over the internet.
- Do not click on unrecognized links or attachments. If you do proceed, verify that the URL is the correct one for the company/service and it has the proper security in place, such as HTTPS.
Many phishing emails pose a sense of urgency or even aggressiveness to prompt a form of intimidation. Any email requesting immediate action should be vetted thoroughly to determine whether or not it is a scam. Also, beware of messages that seek to tempt users into opening an attachment or visiting a link. For example, an attachment titled “Fix your account now” may draw the question “What is wrong with my account?” and prompt you to click a suspicious link.
Cybersecurity Brief
In this week’s Cybersecurity Brief:
Lithuania Suffers a Series of DDOS Attacks Following The Ban of Kaliningrad Imports

Earlier today, Russian hacking group Killnet claimed responsibility for a denial-of-service (DDOS) cyberattack against Lithuania. This news breaks following reports earlier this month where Lithuania banned the transit of goods through their country to the Russian enclave of Kaliningrad, situated between Poland and Lithuania with no border touching Russian soil. State and private institutions in Lithuania were taken offline early Monday, June 27, 2022, after the National Cyber Security Centre released a statement detailing an ongoing cyberattack.
The spokesperson for Killnet announced that this series of DDOS attacks are in direct retaliation to the blocking of transit of goods sanctioned by the EU destined for Kaliningrad. Earlier this month, Moscow released a statement promising a “practical” response to the parties responsible for banning the movement of goods into Russia. Russia’s foreign ministry has since demanded a cease of the goods embargo of coal, construction materials, technology, and metals into their country. The ministry reaffirmed this sentiment in this statement:
“If in the near future cargo transit between the Kaliningrad region and the rest of the territory of the Russian Federation through Lithuania is not restored in full, then Russia reserves the right to take actions to protect its national interests.”
Information Security experts expect more DDOS attacks like this to increase in frequency in the new few weeks if Russia’s demands are not met promptly. Denial-of-service attacks work by flooding a website or server with a massive amount of fake traffic. These attacks overload the system, eventually shutting them offline, and can persist with continued efforts by the hacking group.
To read more about this article, click here.
Carnival Cruise Lines Hit With $5,000,000 Fine for Cybersecurity Incidents

The New York State Department of Financial Services levied a $5 million penalty on Carnival Corp, owners of the globally recognized Carnival Cruises brand, earlier this month. These sanctions follow previous reports that Carnival Corp. has misreported and not adequately responded to numerous cyber-attacks they have suffered over the last few years. In recent months, government and state regulators have urged corporations to treat matters of cybersecurity with urgency and have indicated fines and penalties will be imposed on companies that do not sure up their reporting and defenses.
In May 2019, Carnival suffered a series of phishing attacks where multiple email accounts were compromised and used to send out mass waves of spam to other employees. In total, threat actors gained access to 124 email accounts hosted on a Microsoft Office 365 email server and were able to extend their reach to other employee accounts. The attack saw a trove of PII exposed with drivers licenses, passport numbers, names, addresses, and social security numbers of multiple employees leaked. Following this incident, Carnival delayed its public response to the breach and failed to notify regulators till April 2020, almost eleven months after the initial cybersecurity incident. However, in 2017 New York imposed a new set of cybersecurity guidelines requiring all businesses to adhere to more stringent security and reporting requirements strictly.
Unfortunately for Carnival, cyber-attacks against their organization persisted with ransomware attacks hitting them in August 2020 and January 2021, a Christmas Day malware attack in 2020, and a second phishing attack in March 2021. Since Carnival recorded four incidents within a three-year period, The New York State Department of Financial Services found that Carnival did not adequately train its employees on cybersecurity basics. Additionally, the regulatory agency found that Carnival’s CISO made false certifications of their readiness from 2018-2020.
Following the announcement of these penalties, Carnival declined to issue any statement of wrongdoing, claiming:
“Carnival routinely reviews security and privacy policies and procedures and implements changes when necessary to enhance information security and privacy controls.”
Carnival has since agreed to a mutual settlement with the DFS and multistate Attorney Generals to create a breach response/notification plan, introduce multifactor authentication for remote email access, and increase their security training for all employees.
For more information check out the rest of the article here.
How Can Netizen Help?
Netizen ensures that security gets built-in and not bolted-on. Providing advanced solutions to protect critical IT infrastructure such as the popular “CISO-as-a-Service” wherein companies can leverage the expertise of executive-level cybersecurity professionals without having to bear the cost of employing them full time.
We also offer compliance support, vulnerability assessments, penetration testing, and more security-related services for businesses of any size and type.
Additionally, Netizen offers an automated and affordable assessment tool that continuously scans systems, websites, applications, and networks to uncover issues. Vulnerability data is then securely analyzed and presented through an easy-to-interpret dashboard to yield actionable risk and compliance information for audiences ranging from IT professionals to executive managers.
Netizen is a CMMI V2.0 Level 3, ISO 9001:2015, and ISO 27001:2013 (Information Security Management) certified company. We are a proud Service-Disabled Veteran-Owned Small Business that is recognized by the U.S. Department of Labor for hiring and retention of military veterans.

















You must be logged in to post a comment.