In a significant cybersecurity development, ESET, a leading Slovak cybersecurity firm, has unearthed a deceptive network of 18 malicious loan apps, collectively known as “SpyLoan.” These apps, designed to exploit users seeking financial services, have been downloaded over 12 million times. Primarily targeting regions in Southeast Asia, Africa, and Latin America, SpyLoan apps masquerade as legitimate loan services but engage in data theft, extortion, and blackmail.
Background and Synopsis
SpyLoan was first identified in 2020 and has seen a resurgence in 2023. ESET’s research revealed that these apps bypassed Google Play’s security measures by adhering to standard privacy policies and KYC norms while masking their true intent.
In order to entice potential victims, SpyLoan apps offer seemingly attractive loan services with high-interest rates. They exploit their users by:
- Harvesting personal and financial information.
- Utilizing the information for blackmail and extortion.
- Employing harassment tactics for loan repayment.
- Threatening to release personal photos and videos on social media.
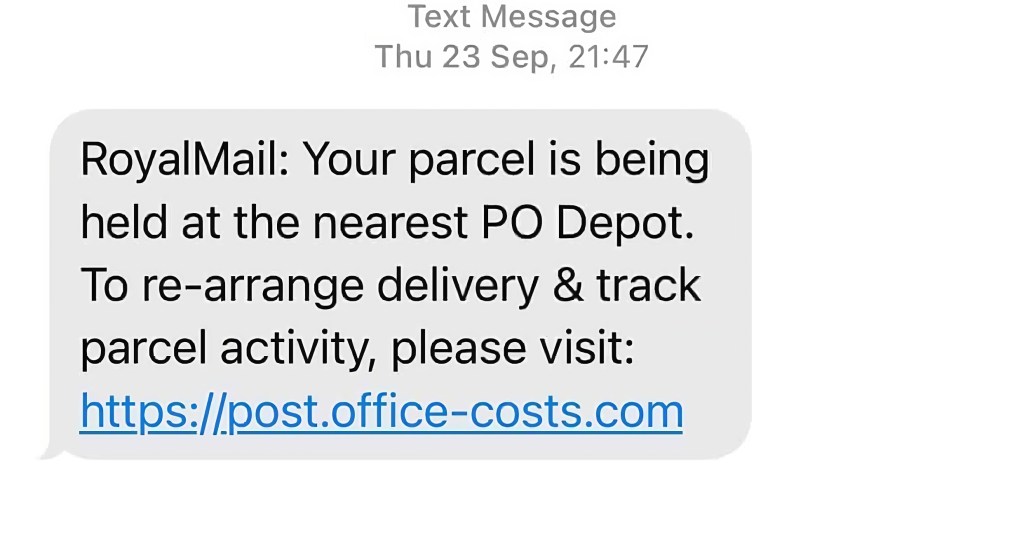
These apps gained traction through various channels, including scam websites, third-party app stores, and even direct downloads from Google Play.
Exploitation of Android Permission System
A key aspect of SpyLoan apps is their abuse of Android’s permission system. These apps request extensive permissions that are unnecessary for their stated purpose of providing financial services. The permissions include access to:
- Contacts and Call Logs: Used to gather personal information about the user and their network, which is then exploited for blackmail and harassment.
- SMS Messages: Enables the apps to intercept incoming messages, which can include sensitive information like one-time passwords (OTPs) or other financial data.
- Media Files and Camera: Access to media files and camera is ostensibly for uploading documents for KYC (Know Your Customer) compliance, but is actually used to gather compromising information.
Misleading Privacy Policies and Websites
The SpyLoan apps are crafted to appear legitimate, with privacy policies and user agreements that mimic those of genuine financial services. However, these policies are intentionally deceptive. As ESET notes, “While these SpyLoan apps technically comply with the requirements of having a privacy policy, their practices clearly go beyond the scope of data collection necessary for providing financial services” (ESET).
These apps often link to websites that are near-replicas of legitimate sites, complete with stolen office environment photos and stock images. This is a tactic designed to create a veneer of authenticity and legitimacy.
Data Harvesting and Blackmail Tactics
Once installed, these apps harvest a wide range of personal data from the device. This includes:
- List of Accounts: Gaining access to account information can lead to identity theft and unauthorized access to other services.
- Device Info and Installed Apps: This information can be used for targeted phishing attacks or to understand the user’s digital behavior better.
- Calendar Events and Local Wi-Fi Network Details: Such details provide further personal information that could be used for social engineering attacks.
- Metadata from Images: This could include location data or other sensitive information embedded in photographs.
The collected data is then used for blackmail and harassment, pressuring victims into making payments under threats of public exposure or ridicule. Some of the SpyLoan apps employ advanced techniques like overlay attacks, where a fraudulent interface is placed over legitimate apps to steal credentials. Furthermore, methods like JsonPacker are used for code obfuscation, making it challenging to detect and analyze the malicious code.
Mitigation Recommendations
To mitigate the risks posed by such threats, users are advised to:
- Scrutinize App Permissions: Be wary of apps that request excessive permissions, especially those unrelated to the app’s functionality.
- Verify App Authenticity: Check the developer’s background and the app’s reviews before downloading.
- Avoid Third-party App Stores: Stick to official app stores like Google Play, as they have more stringent security checks.
- Stay Informed: Be aware of the latest cybersecurity threats and tactics used by cybercriminals.
List of Malicious Apps
The following are the identified SpyLoan apps, which have now been removed from the Google Play Store:
- AA Kredit: इंस्टेंट लोन ऐप (com.aa.kredit.android)
- Amor Cash: Préstamos Sin Buró (com.amorcash.credito.prestamo)
- Oro Préstamo – Efectivo rápido (com.app.lo.go)
- Cashwow (com.cashwow.cow.eg)
- CrediBus Préstamos de crédito (com.dinero.profin.prestamo.credito.credit.credibus.loan.efectivo.cash)
- ยืมด้วยความมั่นใจ – ยืมด่วน (com.flashloan.wsft)
- PréstamosCrédito – GuayabaCash (com.guayaba.cash.okredito.mx.tala)
- Préstamos De Crédito-YumiCash (com.loan.cash.credit.tala.prestmo.fast.branch.mextamo)
- Go Crédito – de confianza (com.mlo.xango)
- Instantáneo Préstamo (com.mmp.optima)
- Cartera grande (com.mxolp.postloan)
- Rápido Crédito (com.okey.prestamo)
- Finupp Lending (com.shuiyiwenhua.gl)
- 4S Cash (com.swefjjghs.weejteop)
- TrueNaira – Online Loan (com.truenaira.cashloan.moneycredit)
- EasyCash (king.credit.ng)
- สินเชื่อปลอดภัย – สะดวก (com.sc.safe.credit)
Conclusion
SpyLoan represents a sophisticated and malicious exploitation of users’ trust in online financial services. Its discovery underscores the importance of vigilance and cybersecurity awareness when engaging with online loan providers. This report serves as a crucial reminder of the risks associated with online financial transactions and the importance of cybersecurity vigilance.
How Can Netizen Help?
Netizen ensures that security gets built-in and not bolted-on. Providing advanced solutions to protect critical IT infrastructure such as the popular “CISO-as-a-Service” wherein companies can leverage the expertise of executive-level cybersecurity professionals without having to bear the cost of employing them full time.
We also offer compliance support, vulnerability assessments, penetration testing, and more security-related services for businesses of any size and type.
Additionally, Netizen offers an automated and affordable assessment tool that continuously scans systems, websites, applications, and networks to uncover issues. Vulnerability data is then securely analyzed and presented through an easy-to-interpret dashboard to yield actionable risk and compliance information for audiences ranging from IT professionals to executive managers.
Netizen is an ISO 27001:2013 (Information Security Management), ISO 9001:2015, and CMMI V 2.0 Level 3 certified company. We are a proud Service-Disabled Veteran-Owned Small Business that is recognized by the U.S. Department of Labor for hiring and retention of military veterans.
Questions or concerns? Feel free to reach out to us any time –
https://www.netizen.net/contact














You must be logged in to post a comment.