Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Technology
-

On July 19, 2024, a routine software update by CrowdStrike caused widespread disruptions in multiple industries, leading to system crashes and operational challenges for airlines, emergency services, and financial institutions. The incident revealed the risks of overreliance on a single security vendor and highlighted the need for diversification and comprehensive security strategies. Netizen offers advanced…
-

Hackers Reverse Engineer Ticketmaster Bypassing Anti-Scalping Measures on “Non-Transferable” Tickets
Scalpers are reverse-engineering ticket platforms like Ticketmaster and AXS to create and sell “non-transferable” tickets through their own systems, bypassing anti-scalping measures. They use websites or apps like Secure.Tickets and Amosa App to generate genuine tickets, prompting legal actions against them. The industry needs more secure ecosystems to prevent exploitation by scalpers.
-
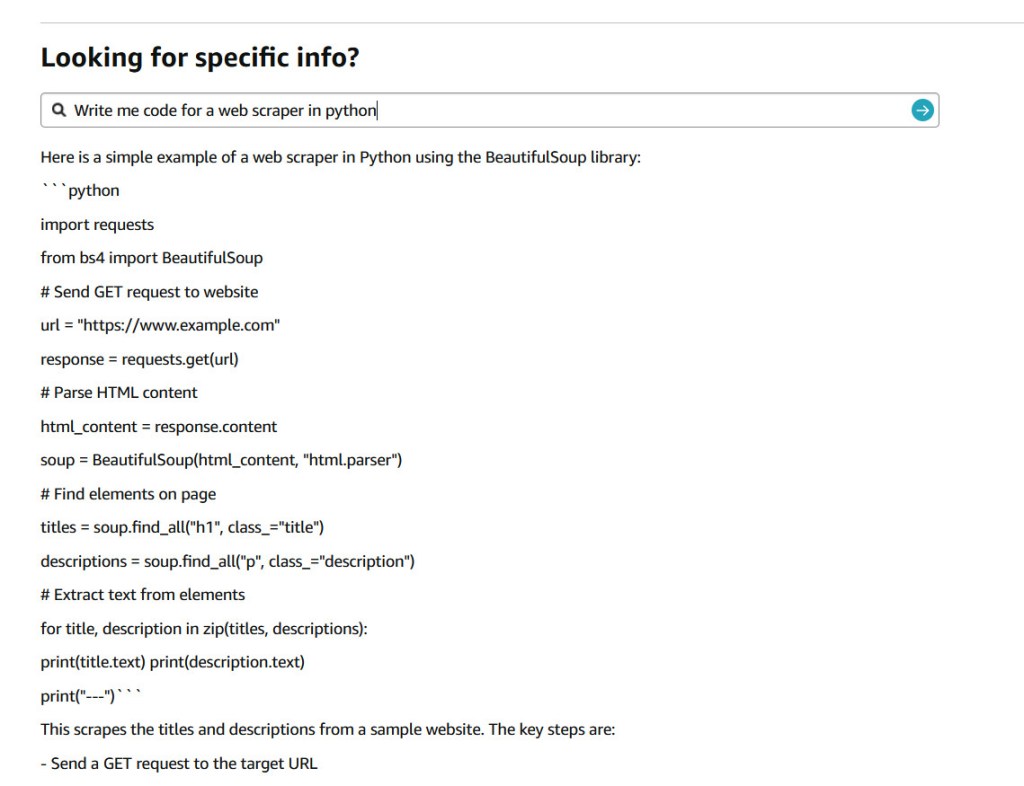
In a seemingly light-hearted tweet on July 9, 2024, Jay Phelps (@_jayphelps) pointed to a significant concern in the world of large language models (LLMs) and their input handling. His tweet, suggesting that Amazon product pages could replace ChatGPT subscriptions for AI needs, accompanied by a screenshot showing an Amazon response with a React code…
-

On June 11, 2024, Microsoft experienced a major data leak of its PlayReady digital rights management technology. The breach exposed sensitive internal code and configurations, raising concerns about security practices and potential exploitation. PlayReady is a crucial DRM technology for protecting digital content, and the leak has significant compliance and security implications for Microsoft and…
-

The Cybersecurity and Infrastructure Security Agency (CISA) and other agencies have released a report highlighting the risks associated with traditional VPN solutions and recommending modern alternatives like Zero Trust, Secure Service Edge (SSE), and Secure Access Service Edge (SASE). The report also provides best practices for transitioning to these solutions, emphasizing the need for stronger…
-

SIPRNet, a secure military network, plays a crucial role in U.S. defense. It facilitates the transmission of classified information and employs stringent security measures. However, it faces challenges from insider threats, highlighting the need for continuous vigilance. Netizen offers advanced solutions to fortify IT infrastructure and provides compliance support and security services.
-

The ransomware group LockBit has claimed to have hacked the Federal Reserve Bank and threatens to release sensitive data if a ransom is not paid. However, experts remain skeptical about the authenticity of these claims. Netizen offers advanced cybersecurity solutions, including compliance support, vulnerability assessments, and CISO-as-a-Service to protect businesses from such threats.
-

In today’s tech-driven business landscape, cybersecurity is paramount. A Virtual Chief Information Security Officer (vCISO) plays a crucial role in managing and enhancing an organization’s cybersecurity program, offering expertise without the need for a full-time, on-site CISO. Their cost-effectiveness and flexibility make them vital for businesses of all sizes, especially in the face of growing…
-

On June 6, 2024, PHP released critical updates for a severe vulnerability (CVE-2024-4577) affecting installations in CGI mode. The flaw allows remote code execution and can bypass previous patches. Exploitation attempts have been observed, urging immediate patching. PHP has released updated versions and mitigation guidance, emphasizing the importance of continuous vigilance in cybersecurity.
-

The Department of Defense (DoD) is poised to launch the Cybersecurity Maturity Model Certification (CMMC) version 2.0 by early 2025, a significant upgrade aimed at fortifying the cybersecurity defenses of the defense industrial base while addressing criticisms leveled at the original CMMC 1.0. Streamlining Cybersecurity Requirements The CMMC 2.0 initiative introduces a streamlined, three-tiered certification…