Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Technology
-
PTaaS combines automated and human assessments to enhance an organization’s cyber posture. It enables continuous testing, offers real-time reporting and strategic recommendations, and includes comprehensive coverage, continuous scanning, customizable testing, and dedicated expertise. PTaaS provides ongoing security management, constant access to security experts, reduced costs, industry standard adherence, swifter turnaround, real-time testing, and more control.…
-

GreyNoise Intelligence has identified “Noise Storms,” involving spoofed web traffic from millions of IPs, suggesting potential links to Chinese state-sponsored actors. These sophisticated attacks manipulate traffic through TTL spoofing and targeted tactics. Despite ongoing investigations, the precise motivations remain unclear, prompting calls for enhanced cybersecurity measures and global collaboration in monitoring these anomalies.
-

Insider threats pose a significant risk to organizations, involving misuse of legitimate access. The Netizen Insider Threat Kill Chain offers a structured approach, highlighting key phases and strategies for effective management. To address common security gaps, a comprehensive approach integrating behavioral analytics, user activity monitoring, and data loss prevention is crucial. Netizen provides advanced solutions,…
-

Network security is crucial for organizational strength, requiring a multi-layered approach to tackle evolving cyber threats. Cloud security demands comprehensive strategies, while IDPS and digital forensics employ advanced technologies to evolve alongside threats. Companies like Netizen offer advanced solutions, including CISO-as-a-Service and compliance support, to protect critical IT infrastructure and ensure regulatory compliance.
-
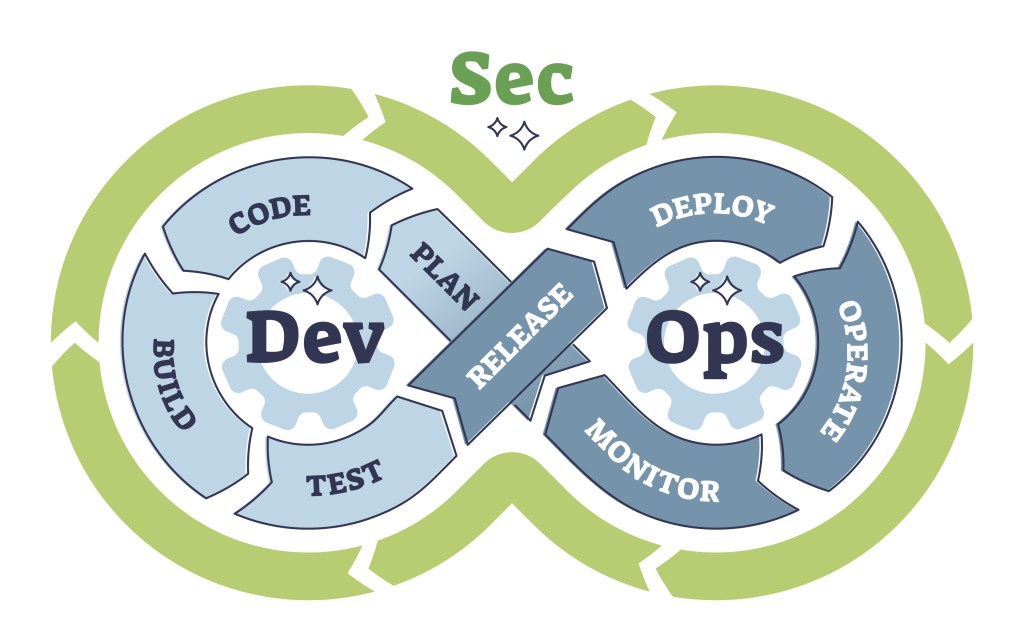
DevOps, DevSecOps, and security posture are essential in modern software development, but often misunderstood. DevOps integrates development and operations to speed up deployment. DevSecOps adds security early in the Agile process and into the containerization and orchestration with automation and thorough documentation. Effective collaboration and cultural change are vital for DevSecOps success.
-

When evaluating ISO 27001 and ISO 27002, it’s essential to understand their distinct roles and purposes in the realm of information security management. Although both standards are closely related, they serve different functions, and recognizing these differences can help you implement them more effectively. General Differences ISO 27001 and ISO 27002 have distinct objectives, which…
-
Volt Typhoon, a Chinese state-sponsored hacking group, has emerged as a significant player in global cybersecurity, focusing particularly on critical infrastructure. This detailed analysis explores Volt Typhoon’s operations, the impacts of its activities, and how we can effectively defend against such threats. Understanding these aspects is crucial for protecting national security and maintaining global stability.…
-
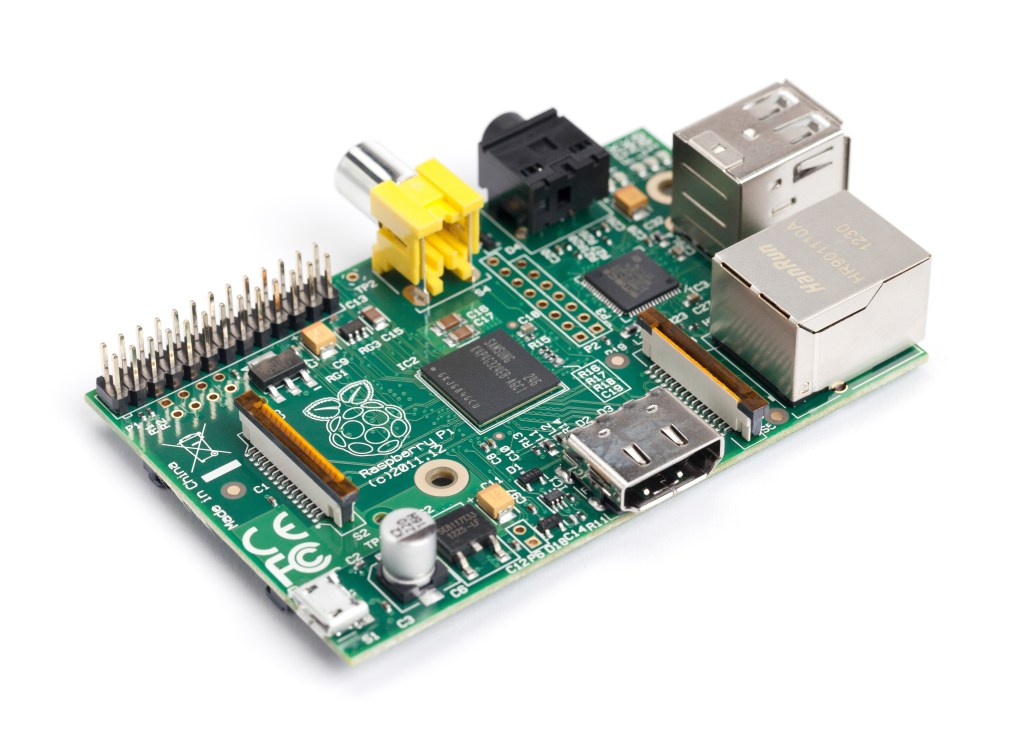
Penetration testing is a flexible skill for cybersecurity analysts. A drop box, like the one built with a Raspberry Pi 3 and TP-Link AC1300 Wi-Fi adapter, provides secure, cost-effective, and easy network access. Netizen offers cybersecurity services, including penetration testing, vulnerability assessments, and automation tools. Visit www.netizen.net/contact for inquiries.
-
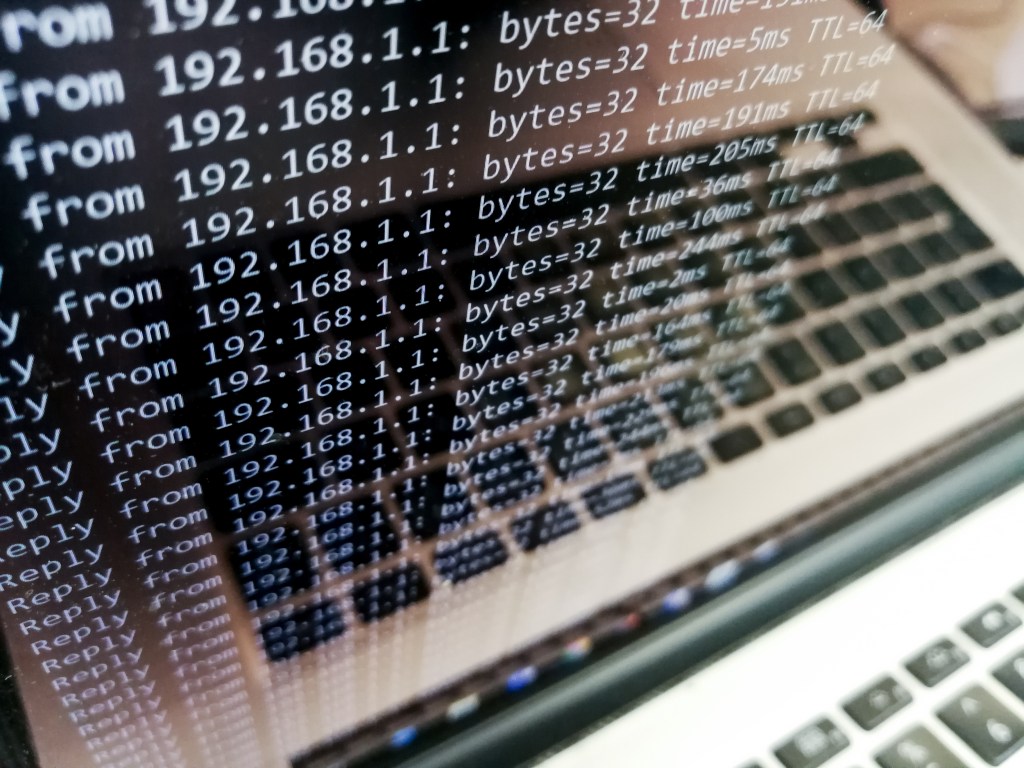
DDoS attacks are a significant threat to internet security that disrupt normal traffic by overwhelming servers. Identifying and mitigating DDoS attacks is crucial. Detection involves monitoring traffic patterns, analyzing sources, and using Intrusion Detection Systems. Mitigation strategies include blackhole routing, rate limiting, Web Application Firewall, and Anycast network diffusion. Netizen offers advanced security solutions and…
-

The cybersecurity industry continues to experience rapid growth, driven by the increasing frequency and sophistication of cyber threats. For those looking to start a career in this field, there are numerous entry-level opportunities that offer a solid foundation and promising career trajectory. This guide provides an overview of some common entry-level cybersecurity roles, highlighting key…