Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Security
-

Recent research from Anthropic-affiliated investigators provides one of the clearest quantitative signals yet that autonomous AI agents have crossed an important threshold in offensive security capability. Using a purpose-built benchmark focused on smart contract exploitation, the study measures success not by abstract accuracy metrics, but by simulated financial loss. The results indicate that current frontier…
-
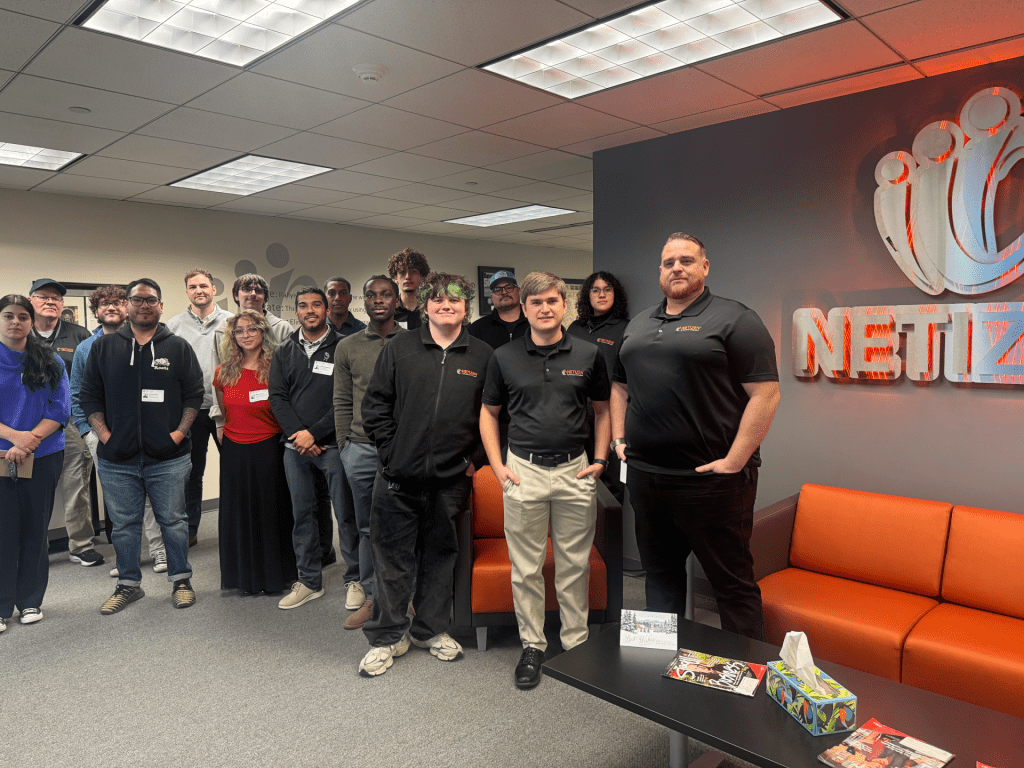
Allentown, PA: Students spent the morning inside Netizen’s 24x7x365 Security Operations Center, observing how analysts monitor systems, investigate alerts, and respond to real security activity as it unfolds. Rather than a simulated exercise, the visit focused on how a production SOC functions day to day, giving students direct exposure to the tools, workflows, and decision-making…
-

Today’s Topics: Kimwolf Android Botnet Spreads Through Exposed ADB and Residential Proxy Networks A large Android botnet known as Kimwolf has quietly compromised more than two million devices by abusing exposed Android Debug Bridge (ADB) services and tunneling through residential proxy networks, based on recent findings from Synthient. The campaign illustrates how misconfigured Android-based devices,…
-

Most security programs still quantify exposure through infrastructure signals. Hosts are scanned. Software is scored. CVEs are triaged. Patch cadence becomes the performance indicator. That system continues to function as designed, yet breach investigations keep showing a disconnect between what vulnerability tools measure and what attackers exploit after authentication occurs. Once valid access is established,…
-

At the executive tier, SOC-as-a-Service represents a structured transfer of detection authority, response execution, investigative control, and portions of post-incident narrative to an external entity. The decision extends far beyond tool selection or coverage expansion. It reshapes how operational security risk is distributed across the organization and its third-party partners. SOCaaS reduces internal staffing volatility,…
-

By early 2026, enterprise security feels very different from just a few years ago. AI agents are now embedded across core workflows, critical vulnerabilities have emerged across widely deployed frameworks with the highest possible severity ratings, and federal standards such as the Cybersecurity Performance Goals 2.0 have reset baseline expectations for security maturity. Risk now…
-

Today’s Topics: Chrome Extensions Found Stealing Credentials from Users Across 170+ Websites Security researchers have uncovered two malicious Google Chrome extensions masquerading as a legitimate network speed-testing tool while secretly intercepting traffic and harvesting user credentials. Both extensions, named Phantom Shuttle and published by the same developer, continue to remain available for download in the…
-

Overview: Phish Tale of the Week Ofteften times phishing campaigns, created by malicious actors, target users by utilizing social engineering. For example, in this text message, the actors are appearing as an unnamed organization. The message politely explains that they’re about to invest in a stock “projected to deliver a 60 percent return this week.”…
-

Today’s Topics: Fake PoCs and AI Noise Are Slowing Real Vulnerability Response The React2Shell vulnerability exposed a growing problem that many security teams are now facing: a flood of “proof-of-concept” (PoC) exploits that either do not work or only apply in narrow edge cases. Some of the most visible examples appear to have been generated…
-

In October 2025, Netizen’s Security Operations Center identified five critical vulnerabilities, including CVE-2025-59287 in Microsoft WSUS and CVE-2025-61882 in Oracle E-Business Suite, posing severe threats. Urgent patching is advised to prevent exploitation, with attackers gaining unauthorized access, control, or deploying malware across networks, affecting data integrity and operational security.