Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: Security
-
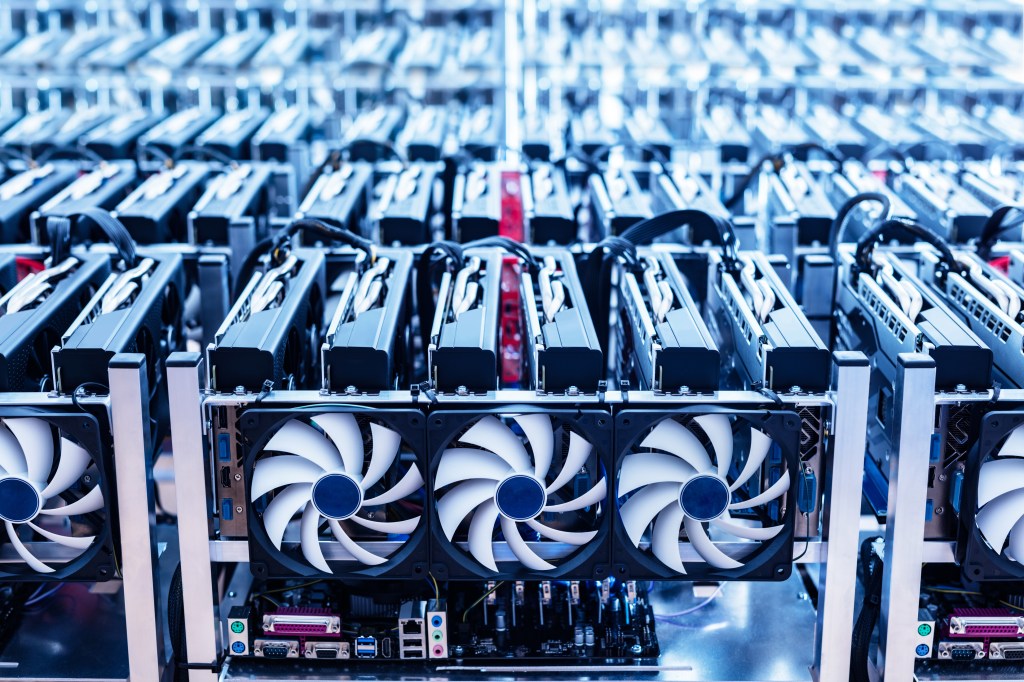
P2PInfect botnet evolves into a multifaceted threat with ransomware and crypto miners, targeting Redis servers and deploying rootkit elements. It seeks profit through illicit access and may operate as a botnet-for-hire service. Lurie Children’s Hospital suffers a ransomware attack, compromising data of 791,000 individuals. Netizen provides advanced security solutions, including compliance support and vulnerability assessments.
-

Cybersecurity researchers from the Qualys Threat Research Unit (TRU) have uncovered a critical flaw in OpenSSH, dubbed ‘regreSSHion’ (CVE-2024-6387), marking a significant threat to the security of Linux-based systems worldwide. This article provides an in-depth exploration of the technical intricacies, impact assessment, and recommended mitigation strategies concerning this vulnerability. Understanding ‘regreSSHion’ ‘RegreSSHion’ is classified as…
-

On June 11, 2024, Microsoft experienced a major data leak of its PlayReady digital rights management technology. The breach exposed sensitive internal code and configurations, raising concerns about security practices and potential exploitation. PlayReady is a crucial DRM technology for protecting digital content, and the leak has significant compliance and security implications for Microsoft and…
-

Security vulnerabilities pose a constant threat to organizational security. Netizen’s Security Operations Center has identified five critical vulnerabilities from June that require immediate patching or addressing. These vulnerabilities affect popular software and devices, emphasizing the need for proactive security measures. Netizen offers comprehensive cybersecurity solutions and support to mitigate such risks. For more information, visit…
-

Identity and Access Management (IAM) is crucial for controlling access to sensitive information, ensuring security, compliance, and efficiency. It centralizes user identities and access rights, streamlining their management and enforcing precise access controls. IAM verifies user identities, manages access, supports productivity, reduces data breach risks, and simplifies compliance with regulations.
-

The ransomware group LockBit has claimed to have hacked the Federal Reserve Bank and threatens to release sensitive data if a ransom is not paid. However, experts remain skeptical about the authenticity of these claims. Netizen offers advanced cybersecurity solutions, including compliance support, vulnerability assessments, and CISO-as-a-Service to protect businesses from such threats.
-

Spanish authorities, with FBI collaboration, arrested 22-year-old British national Tyler Buchanan in Palma de Mallorca. The alleged ringleader of the Scattered Spider hacking group is implicated in high-profile cyber-attacks and cryptocurrency theft. The investigation reveals Buchanan’s use of social engineering and phishing, and ongoing efforts to uncover further insights into Scattered Spider’s activities.
-

Velvet Ant, a Chinese cyberespionage group, used custom malware to target F5 BIG-IP appliances in a campaign aiming to breach and persist within networks. They accessed internal servers, deployed remote access tools, and maintained access for three years. To mitigate such attacks, organizations should limit outbound internet traffic, restrict lateral movement, and enhance security hardening…
-

In today’s tech-driven business landscape, cybersecurity is paramount. A Virtual Chief Information Security Officer (vCISO) plays a crucial role in managing and enhancing an organization’s cybersecurity program, offering expertise without the need for a full-time, on-site CISO. Their cost-effectiveness and flexibility make them vital for businesses of all sizes, especially in the face of growing…
-

London authorities recently uncovered a sophisticated smishing scheme using a makeshift cellphone tower to send malicious text messages, marking an alarming escalation in digital fraud. Two arrests have been made, emphasizing the need for collaborative efforts to combat cybercrime. Public vigilance and proactive measures are urged, such as avoiding clicking links and reporting suspicious messages.