Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
- Iran-Linked Group Claims Cyberattack on U.S. Medical Technology Company Stryker
- Microsoft March 2026 Patch Tuesday Fixes 79 Flaws, Including Two Publicly Disclosed Zero-Days
- Netizen: Monday Security Brief (3/9/2026)
- EDR Integration in SOCaaS: The Control Point That Matters
- Conditional Access vs Zero Trust: What’s the Difference?
about
Category: Government IT
-
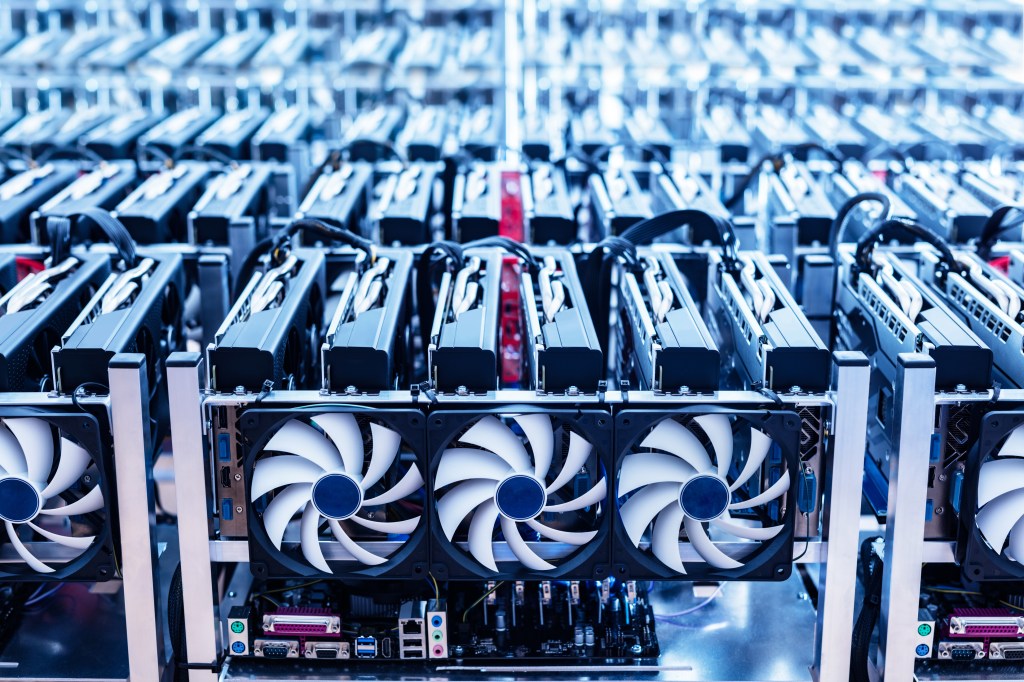
P2PInfect botnet evolves into a multifaceted threat with ransomware and crypto miners, targeting Redis servers and deploying rootkit elements. It seeks profit through illicit access and may operate as a botnet-for-hire service. Lurie Children’s Hospital suffers a ransomware attack, compromising data of 791,000 individuals. Netizen provides advanced security solutions, including compliance support and vulnerability assessments.
-

The Cybersecurity and Infrastructure Security Agency (CISA) and other agencies have released a report highlighting the risks associated with traditional VPN solutions and recommending modern alternatives like Zero Trust, Secure Service Edge (SSE), and Secure Access Service Edge (SASE). The report also provides best practices for transitioning to these solutions, emphasizing the need for stronger…
-

SIPRNet, a secure military network, plays a crucial role in U.S. defense. It facilitates the transmission of classified information and employs stringent security measures. However, it faces challenges from insider threats, highlighting the need for continuous vigilance. Netizen offers advanced solutions to fortify IT infrastructure and provides compliance support and security services.
-

The ransomware group LockBit has claimed to have hacked the Federal Reserve Bank and threatens to release sensitive data if a ransom is not paid. However, experts remain skeptical about the authenticity of these claims. Netizen offers advanced cybersecurity solutions, including compliance support, vulnerability assessments, and CISO-as-a-Service to protect businesses from such threats.
-

In today’s tech-driven business landscape, cybersecurity is paramount. A Virtual Chief Information Security Officer (vCISO) plays a crucial role in managing and enhancing an organization’s cybersecurity program, offering expertise without the need for a full-time, on-site CISO. Their cost-effectiveness and flexibility make them vital for businesses of all sizes, especially in the face of growing…
-

London authorities recently uncovered a sophisticated smishing scheme using a makeshift cellphone tower to send malicious text messages, marking an alarming escalation in digital fraud. Two arrests have been made, emphasizing the need for collaborative efforts to combat cybercrime. Public vigilance and proactive measures are urged, such as avoiding clicking links and reporting suspicious messages.
-

The Department of Defense (DoD) is poised to launch the Cybersecurity Maturity Model Certification (CMMC) version 2.0 by early 2025, a significant upgrade aimed at fortifying the cybersecurity defenses of the defense industrial base while addressing criticisms leveled at the original CMMC 1.0. Streamlining Cybersecurity Requirements The CMMC 2.0 initiative introduces a streamlined, three-tiered certification…
-

Phishing attacks have become a growing concern in recent years, with cybercriminals employing increasingly sophisticated methods to access sensitive corporate data. These attacks typically involve deceiving users into clicking on malicious links or opening harmful attachments, leading to the theft of sensitive information or the compromise of corporate systems. This article explores the benefits of…
-

Federal agencies are enhancing data routing security measures to protect against cyberattacks. By implementing the Border Gateway Protocol (BGP) and leveraging encryption frameworks like RPKI, they aim to thwart hijacking attempts. National Cyber Director Harry Coker emphasized the importance of cybersecurity partnerships and addressed the need to secure space systems and build a robust cybersecurity…
-
Overview: Phish Tale of the Week Often times phishing campaigns, created by malicious actors, target users by utilizing social engineering. For example, in this email, the actors are appearing as WalletConnect. The message politely gives us an opportunity for a cryptocurrency airdrop, saying we’re “invited” and that “it’s a rare opportunity” for us. It seems…