Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
- Iran-Linked Group Claims Cyberattack on U.S. Medical Technology Company Stryker
- Microsoft March 2026 Patch Tuesday Fixes 79 Flaws, Including Two Publicly Disclosed Zero-Days
- Netizen: Monday Security Brief (3/9/2026)
- EDR Integration in SOCaaS: The Control Point That Matters
- Conditional Access vs Zero Trust: What’s the Difference?
about
Category: Government IT
-

OpenAI recently shut down an Iranian influence campaign called Storm-2035, using ChatGPT to sway opinions on US political issues and global events. Flint, Michigan suffered a ransomware attack, affecting online services. Amid these challenges, Netizen offers advanced security solutions, compliance support, and automated assessment tools to protect IT infrastructure and mitigate risks.
-

Firewalls are essential for data protection. Next Generation Firewalls (NGFWs) go beyond traditional firewalls, offering advanced features like application control, intrusion prevention, and cloud-delivered threat intelligence. NGFWs provide comprehensive security, addressing modern cyber threats effectively. While traditional firewalls have their place, NGFWs are superior for robust network protection in today’s digital landscape.
-

A cybersecurity breach at National Public Data has exposed 2.7 billion records of US citizens, leading to a class-action lawsuit. The lawsuit argues the company failed to protect personal information and benefited economically from collecting it. Malicious browser extensions have also been identified as a new vector for malware distribution, affecting at least 300,000 users.…
-

The Policy Enforcement Point (PEP) is a crucial part of the Attribute-Based Access Control (ABAC) architecture, ensuring consistent access control and security for enterprise data. It intercepts user requests, evaluates attributes, and communicates with the Policy Decision Point (PDP) to determine access, providing robust security for modern applications.
-

Switzerland has enacted EMBAG, mandating open-source software use in the public sector, promoting transparency and security. The US has a cautious approach due to security concerns, but may need to reassess. Open source fosters innovation, cost savings, and enhances security.
-

A DDoS attack caused a 10-hour global outage for Microsoft services, impacting various platforms and organizations. Chinese hackers targeted Japanese entities with advanced LODEINFO malware. Netizen offers advanced cybersecurity solutions, including “CISO-as-a-Service” and automated assessment tools for continuous system scanning and risk analysis, ensuring robust protection for businesses.
-

This content covers phishing tactics targeting Amazon users, EU scrutiny of Meta, and a federal recovery from a CrowdStrike outage. It advises caution with unsolicited links and attachments, scrutinizing messages, and not divulging personal information online. It also highlights Netizen’s cybersecurity solutions including CISO-as-a-Service and vulnerability assessments.
-

The Federal Bureau of Investigation (FBI) has announced the successful execution of Operation Endgame, a groundbreaking multinational cyber operation aimed at dismantling a sophisticated network of cybercriminals. This unprecedented initiative involved coordinated efforts from law enforcement agencies across the United States, Denmark, France, Germany, the Netherlands, the United Kingdom, and other countries, with crucial support…
-

A federal court ruled that a company can be held liable for a data breach at its law firm, permitting a negligence claim against Mondelez Global LLC. This underscores the importance of thorough third-party risk management and data security measures, including evaluations, data minimization, contractual safeguards, continuous monitoring, and robust incident response.
-
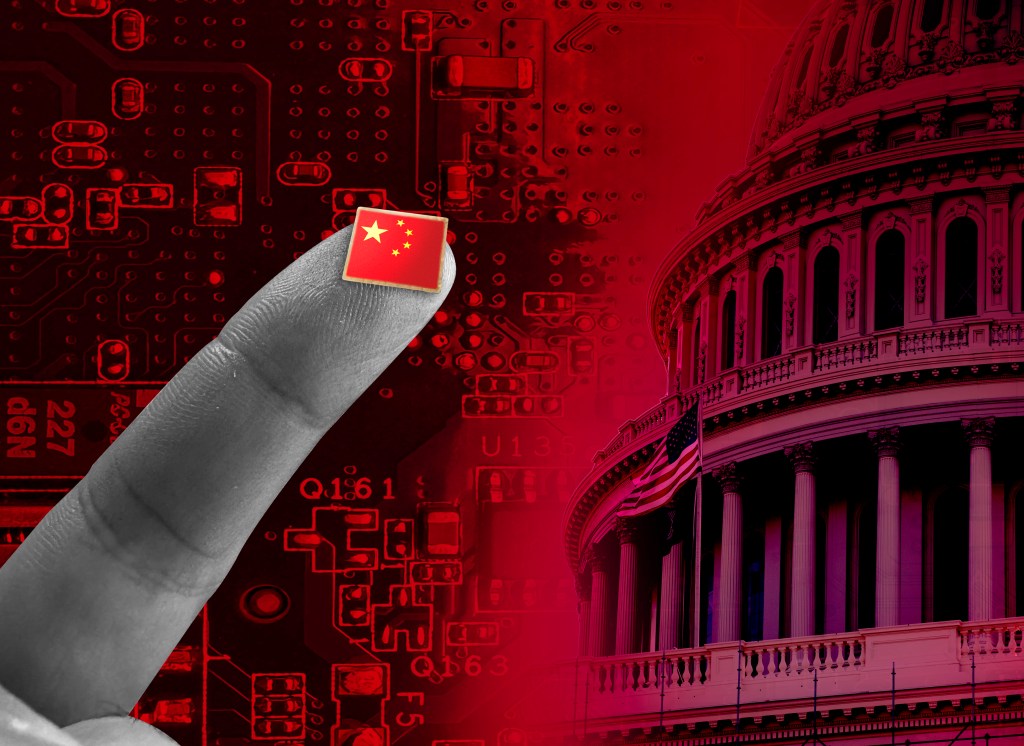
Chinese state-backed hackers have exploited a newly patched zero-day vulnerability in Cisco Nexus switches, allowing them to execute arbitrary commands as root. The attackers’ custom malware facilitated remote access to compromised devices. Security measures such as regular patching, strong passwords, restricted admin access, and enhanced monitoring are recommended to mitigate such threats.