Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
- Iran-Linked Group Claims Cyberattack on U.S. Medical Technology Company Stryker
- Microsoft March 2026 Patch Tuesday Fixes 79 Flaws, Including Two Publicly Disclosed Zero-Days
- Netizen: Monday Security Brief (3/9/2026)
- EDR Integration in SOCaaS: The Control Point That Matters
- Conditional Access vs Zero Trust: What’s the Difference?
about
Category: Government IT
-

GreyNoise Intelligence has identified “Noise Storms,” involving spoofed web traffic from millions of IPs, suggesting potential links to Chinese state-sponsored actors. These sophisticated attacks manipulate traffic through TTL spoofing and targeted tactics. Despite ongoing investigations, the precise motivations remain unclear, prompting calls for enhanced cybersecurity measures and global collaboration in monitoring these anomalies.
-

Windows 11 aims to redefine how anti-malware tools interact with the Windows kernel to enhance system resilience and security following a disruptive IT incident. Meanwhile, the Hadooken malware targets Linux systems with cryptocurrency mining and DDoS attacks, requiring vigilance and mitigation efforts. Netizen offers advanced security solutions, including CISO-as-a-Service, compliance support, and automated vulnerability assessment…
-

Today’s Topics: CISA Responds to Controversial ‘Airport Security Bypass’ Vulnerability In late August 2024, cybersecurity researchers Ian Carroll and Sam Curry revealed a potentially alarming security flaw within FlyCASS, a third-party web-based application utilized by smaller airlines as part of the Cockpit Access Security System (CASS) and Known Crewmember (KCM) programs. These programs play a…
-

When evaluating ISO 27001 and ISO 27002, it’s essential to understand their distinct roles and purposes in the realm of information security management. Although both standards are closely related, they serve different functions, and recognizing these differences can help you implement them more effectively. General Differences ISO 27001 and ISO 27002 have distinct objectives, which…
-

The National Institute of Standards and Technology (NIST) has recently unveiled three new Federal Information Processing Standards (FIPS) aimed at addressing the emerging challenges posed by quantum computing. These standards—FIPS 203, 204, and 205—represent a pivotal advancement in strengthening the resilience of digital communications against future quantum threats, while also bolstering current cryptographic practices. Overview…
-

This content covers phishing tactics targeting Amazon users, EU scrutiny of Meta, and a federal recovery from a CrowdStrike outage. It advises caution with unsolicited links and attachments, scrutinizing messages, and not divulging personal information online. It also highlights Netizen’s cybersecurity solutions including CISO-as-a-Service and vulnerability assessments.
-

The FBI’s shortcomings in securing sensitive storage media were exposed in an OIG audit, indicating improper handling and storage of decommissioned devices. Meanwhile, Pavel Durov, CEO of Telegram, was arrested in France for alleged failure to moderate criminal activities on the platform.
-

SOC 2 (System and Organization Controls 2) is a security framework developed by the American Institute of Certified Public Accountants (AICPA). It outlines the criteria for managing customer data based on five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. SOC 2 compliance is critical for organizations that handle sensitive customer information, ensuring…
-
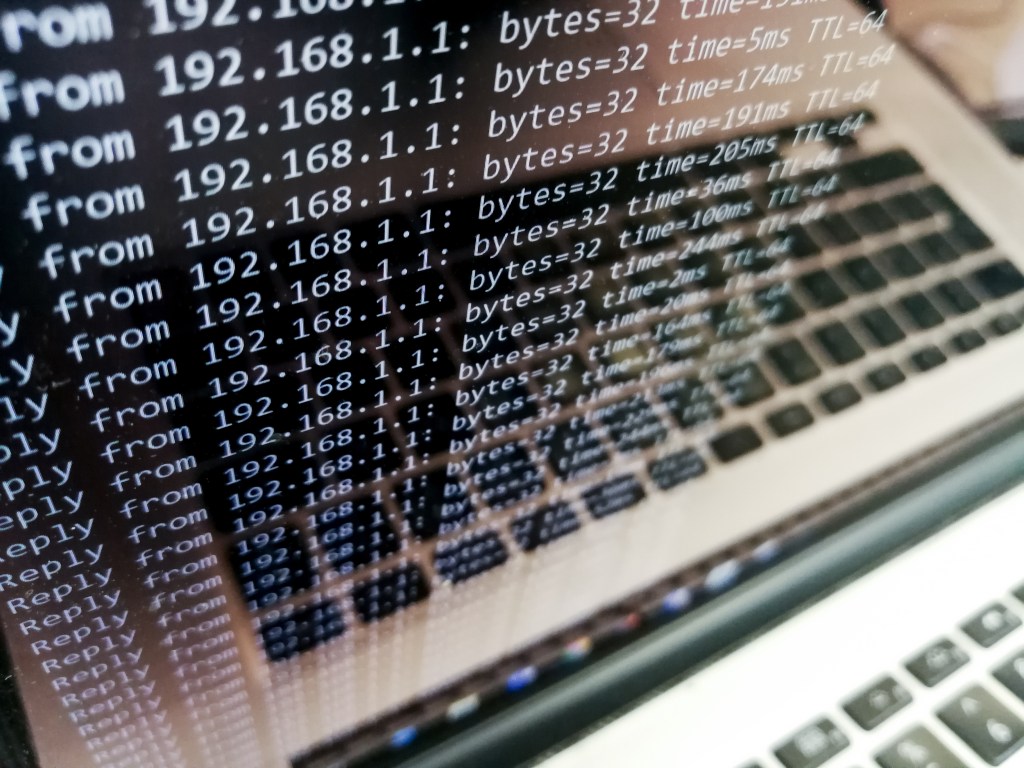
DDoS attacks are a significant threat to internet security that disrupt normal traffic by overwhelming servers. Identifying and mitigating DDoS attacks is crucial. Detection involves monitoring traffic patterns, analyzing sources, and using Intrusion Detection Systems. Mitigation strategies include blackhole routing, rate limiting, Web Application Firewall, and Anycast network diffusion. Netizen offers advanced security solutions and…
-

A recent Windows zero-day vulnerability (CVE-2024-38193) was exploited by North Korea’s Lazarus APT group, allowing the installation of the FudModule rootkit. This advanced breach highlights the urgent need for organizations to apply patches promptly and strengthen their security measures to combat increasingly sophisticated cyber threats. Netizen offers advanced security solutions and support services.