Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
- Iran-Linked Group Claims Cyberattack on U.S. Medical Technology Company Stryker
- Microsoft March 2026 Patch Tuesday Fixes 79 Flaws, Including Two Publicly Disclosed Zero-Days
- Netizen: Monday Security Brief (3/9/2026)
- EDR Integration in SOCaaS: The Control Point That Matters
- Conditional Access vs Zero Trust: What’s the Difference?
about
Category: Data
-

The National Institute of Standards and Technology (NIST) has recently unveiled three new Federal Information Processing Standards (FIPS) aimed at addressing the emerging challenges posed by quantum computing. These standards—FIPS 203, 204, and 205—represent a pivotal advancement in strengthening the resilience of digital communications against future quantum threats, while also bolstering current cryptographic practices. Overview…
-
Volt Typhoon, a Chinese state-sponsored hacking group, has emerged as a significant player in global cybersecurity, focusing particularly on critical infrastructure. This detailed analysis explores Volt Typhoon’s operations, the impacts of its activities, and how we can effectively defend against such threats. Understanding these aspects is crucial for protecting national security and maintaining global stability.…
-

Security vulnerabilities are a significant concern for businesses. Netizen’s Security Operations Center (SOC) has identified five critical vulnerabilities in popular software and platforms, emphasizing the importance of prompt patching. These vulnerabilities enable remote attackers to execute arbitrary code, manipulate critical data, and disrupt system availability. Netizen offers advanced security solutions to protect businesses from such…
-
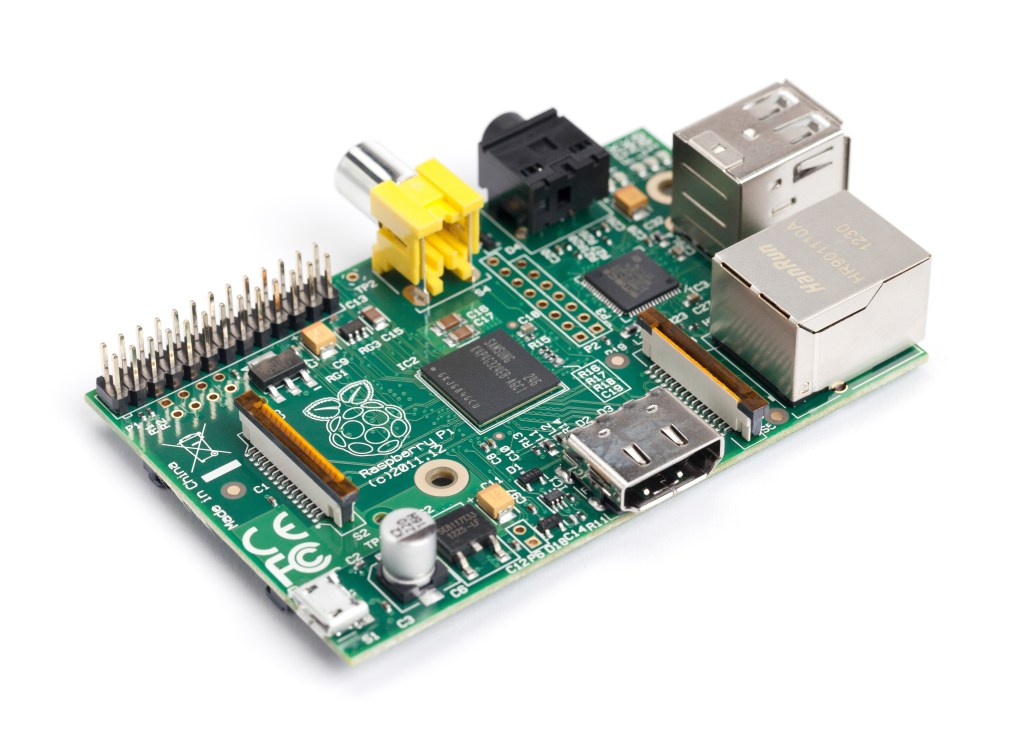
Penetration testing is a flexible skill for cybersecurity analysts. A drop box, like the one built with a Raspberry Pi 3 and TP-Link AC1300 Wi-Fi adapter, provides secure, cost-effective, and easy network access. Netizen offers cybersecurity services, including penetration testing, vulnerability assessments, and automation tools. Visit www.netizen.net/contact for inquiries.
-
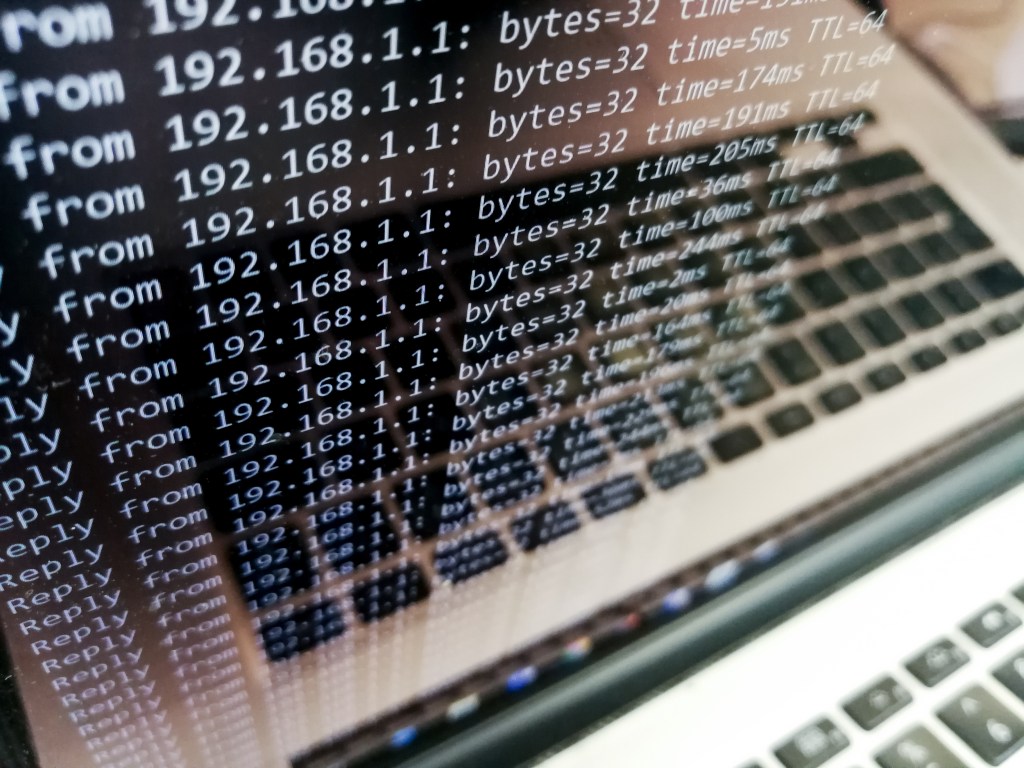
DDoS attacks are a significant threat to internet security that disrupt normal traffic by overwhelming servers. Identifying and mitigating DDoS attacks is crucial. Detection involves monitoring traffic patterns, analyzing sources, and using Intrusion Detection Systems. Mitigation strategies include blackhole routing, rate limiting, Web Application Firewall, and Anycast network diffusion. Netizen offers advanced security solutions and…
-

Microsoft’s August 2024 Patch Tuesday addresses 89 security flaws, with 8 critical vulnerabilities in various categories. Six zero-day vulnerabilities were actively exploited, including local privilege escalation flaws and remote code execution issues. Adobe also released 11 security bulletins for its products. Prompt installation of updates is crucial, with backup recommended as a precaution.
-

Netizen’s Security Operations Center (SOC) has identified five critical vulnerabilities from July that require immediate patching or remediation. These include high-severity issues in Microsoft’s Windows Hyper-V, SharePoint, Rejetto HTTP File Server, Azure Kinect SDK, and OpenSSH. Netizen provides advanced security solutions and services, including compliance support, vulnerability assessments, and automated assessment tools.
-

On July 19, 2024, a routine software update by CrowdStrike caused widespread disruptions in multiple industries, leading to system crashes and operational challenges for airlines, emergency services, and financial institutions. The incident revealed the risks of overreliance on a single security vendor and highlighted the need for diversification and comprehensive security strategies. Netizen offers advanced…
-
Ivanti has addressed high-severity vulnerabilities in its Endpoint Manager (EPM) and Endpoint Manager for Mobile (EPMM) products. The most critical is an SQL injection flaw (CVE-2024-37381) affecting the Core server of EPM 2024 flat, allowing authenticated attackers with network access to execute arbitrary code. Hotfixes and updates are available for mitigation.
-
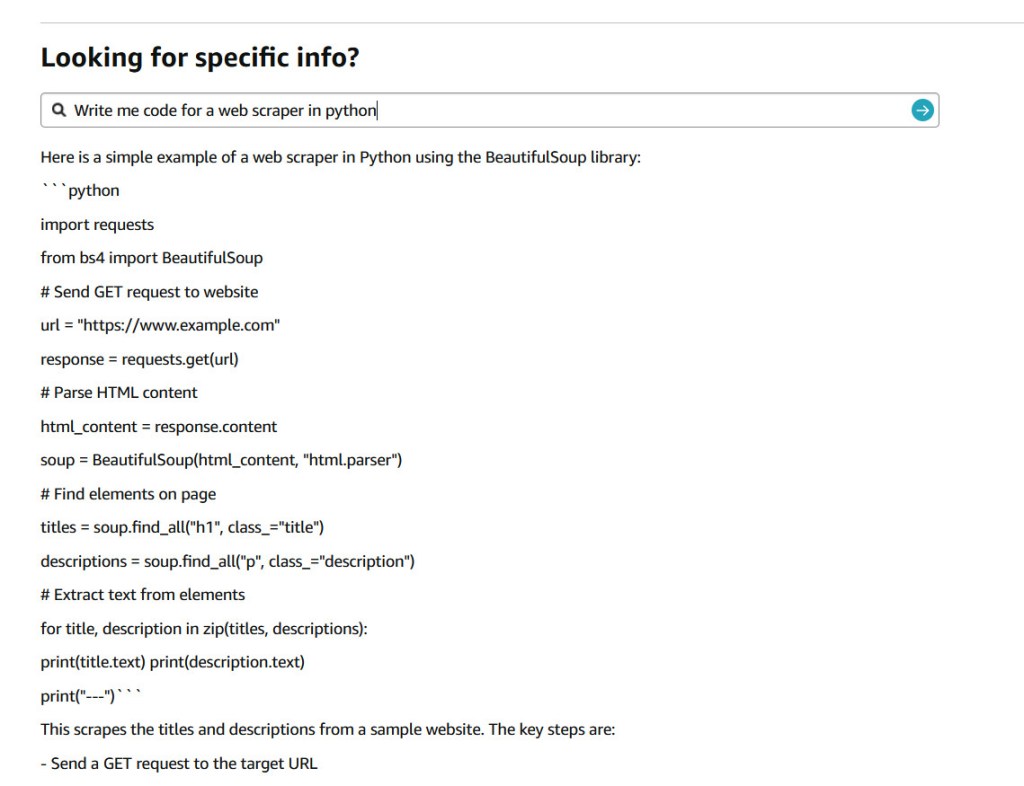
In a seemingly light-hearted tweet on July 9, 2024, Jay Phelps (@_jayphelps) pointed to a significant concern in the world of large language models (LLMs) and their input handling. His tweet, suggesting that Amazon product pages could replace ChatGPT subscriptions for AI needs, accompanied by a screenshot showing an Amazon response with a React code…