Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
- Exchange Online Admin Abuse: What to Watch For
- Netizen: Monday Security Brief (3/16/2026)
- SOCaaS for Organizations Without a CISO
- Iran-Linked Group Claims Cyberattack on U.S. Medical Technology Company Stryker
- Microsoft March 2026 Patch Tuesday Fixes 79 Flaws, Including Two Publicly Disclosed Zero-Days
about
Category: CyberSecurity
-

PCI DSS is crucial for businesses handling credit card info. Common mistakes include neglecting security assessments, storing data incorrectly, weak passwords, lack of employee training, non-compliant third-party vendors, and more. To ensure compliance, businesses can consult cybersecurity experts and utilize Netizen’s services for built-in security and compliance support.
-

Microsoft Corp. is set to unveil artificial intelligence tools on April 1, aimed at enhancing the capabilities of cybersecurity professionals. These tools, developed in partnership with OpenAI, will assist in summarizing suspicious incidents and uncovering hackers’ methods. Dubbed Copilot for Security, this suite of AI tools was unveiled approximately a year ago and has since…
-

Over the last half-decade, TikTok has swiftly climbed to a leading position within the realm of social media, captivating a worldwide audience with its short, intriguing video content. Owned by the Chinese technological behemoth ByteDance, TikTok has been the focus of intense international scrutiny and debate, mainly from Western governments. The heart of this debate…
-

Fortinet has recently taken steps to strengthen its cybersecurity posture by patching a critical flaw in the FortiClient Enterprise Management Server (EMS) software, which had left servers vulnerable to remote code execution (RCE) attacks. This effort reflects Fortinet’s commitment to addressing security vulnerabilities promptly to protect against potential cyber threats. In addressing various security concerns,…
-

How can developers ensure their software stands strong against the barrage of cyber threats today? The key lies in secure coding practices, which are crucial for building software that is not only functional but also resilient to potential security breaches. This article examines secure coding’s importance and unfolds through practical strategies like code minification, obfuscation,…
-

In the rapidly expanding world of the Internet of Things (IoT), our lives are increasingly interconnected with smart devices that promise to make daily tasks more efficient. From smart thermostats regulating our homes to wearables monitoring our health, the IoT era is reshaping how we interact with technology. Yet, this convenience comes with a price…
-

As we delve deeper into 2024, ransomware continues to morph, presenting new challenges for cybersecurity professionals worldwide. This evolving landscape requires constant vigilance and adaptation of defense strategies. Here, we explore the most significant trends in ransomware evolution and how they’re shaping the cyber threat horizon. Double Extortion and Beyond Ransomware attacks are increasingly incorporating…
-

Recently, the healthcare sector faced a significant cybersecurity challenge when Change Healthcare, a prominent healthcare payment and management solutions provider, became the target of a sophisticated cyberattack by ransomware group BlackCat. This blog post offers an in-depth analysis of the incident, exploring the specifics of the breach, identifying the perpetrators, and assessing its profound impact…
-
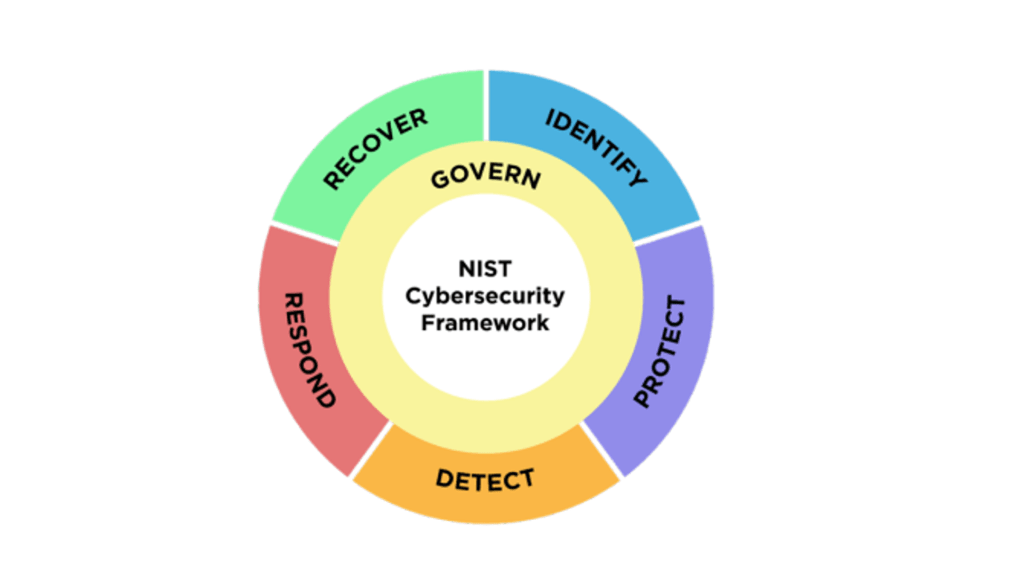
The National Institute of Standards and Technology (NIST) has officially released version 2.0 of its landmark Cybersecurity Framework (CSF), marking its first major update since the framework’s inception in 2014. The revised framework introduces significant enhancements designed to extend its applicability and effectiveness across a broader spectrum of organizations, ranging from the smallest schools and…
-
Overview: Phish Tale of the Week Often times phishing/smishing campaigns, created by malicious actors, target users by utilizing social engineering. For example, in this text message, the actors are appearing as Coinbase and informing you that action needs to be taken regarding your account. The message first prompts you with a notification that your account…