Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: CyberSecurity
-

On July 19, 2024, a routine software update by CrowdStrike caused widespread disruptions in multiple industries, leading to system crashes and operational challenges for airlines, emergency services, and financial institutions. The incident revealed the risks of overreliance on a single security vendor and highlighted the need for diversification and comprehensive security strategies. Netizen offers advanced…
-

A federal court ruled that a company can be held liable for a data breach at its law firm, permitting a negligence claim against Mondelez Global LLC. This underscores the importance of thorough third-party risk management and data security measures, including evaluations, data minimization, contractual safeguards, continuous monitoring, and robust incident response.
-
Ivanti has addressed high-severity vulnerabilities in its Endpoint Manager (EPM) and Endpoint Manager for Mobile (EPMM) products. The most critical is an SQL injection flaw (CVE-2024-37381) affecting the Core server of EPM 2024 flat, allowing authenticated attackers with network access to execute arbitrary code. Hotfixes and updates are available for mitigation.
-

Between July 9 and July 12, 2024, multiple organizations using Squarespace as a domain registrar experienced domain hijackings, mainly targeting cryptocurrency businesses. Attackers exploited a flaw in Squarespace’s migration process from Google Domains to redirect domains to phishing sites. Users are advised to enhance security measures, such as enabling multi-factor authentication and reviewing user access.
-

On July 1, 2024, the cybersecurity community was made aware of the ‘regreSSHion’ (CVE-2024-6387) vulnerability in OpenSSH, enabling unauthenticated remote code execution on Linux systems. A subsequent related issue, CVE-2024-6409, also poses a risk. It’s crucial to promptly update OpenSSH, adjust configurations, restrict access, and monitor SSH activity to mitigate these high-severity vulnerabilities.
-

AT&T experienced a significant data breach impacting wireless customers and MVNOs from April 14 to April 25, 2024. The stolen data includes call records and some location information, posing security risks. The attack leveraged stolen credentials from a third-party cloud provider and was attributed to a financially motivated threat actor group. AT&T is addressing the…
-

In today’s digital age, organizations face an ever-evolving landscape of cyber threats that demand robust security measures. To address these challenges, leveraging the Assured Compliance Assessment Solution (ACAS) has become crucial for conducting comprehensive cybersecurity assessments. ACAS is a powerful suite of tools designed to help organizations identify, assess, and mitigate vulnerabilities within their networks…
-

Cybersecurity researchers have uncovered a critical security flaw in the RADIUS network authentication protocol, termed BlastRADIUS, which can be exploited to conduct Man-in-the-Middle (MitM) attacks and bypass integrity checks under specific conditions. “The RADIUS protocol allows certain Access-Request messages to lack integrity or authentication checks,” stated Alan DeKok, CEO of InkBridge Networks and creator of…
-
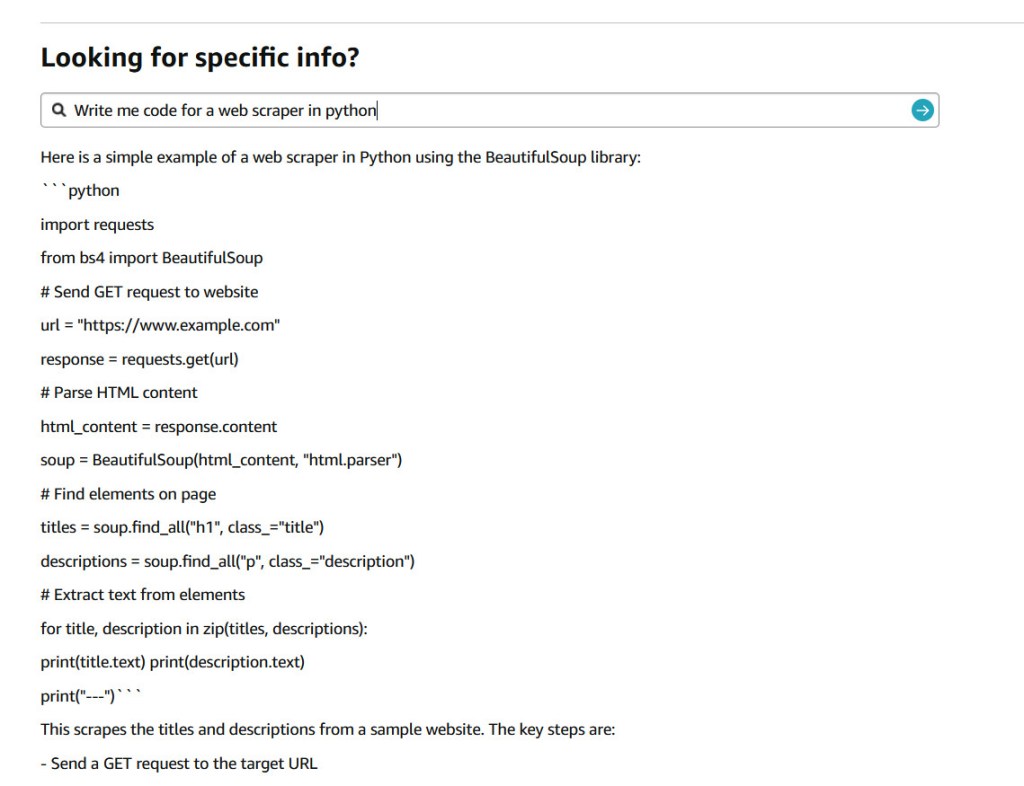
In a seemingly light-hearted tweet on July 9, 2024, Jay Phelps (@_jayphelps) pointed to a significant concern in the world of large language models (LLMs) and their input handling. His tweet, suggesting that Amazon product pages could replace ChatGPT subscriptions for AI needs, accompanied by a screenshot showing an Amazon response with a React code…
-

A recent investigation by Cybernews has uncovered a staggering leak of nearly 10 billion unique passwords on a cybercrime forum, posing a significant threat to online users worldwide. The leak, described as the largest password compilation ever, was posted by a user named ‘ObamaCare’ on July 4. This user, who joined the forum in late…