Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
Category: CyberSecurity
-
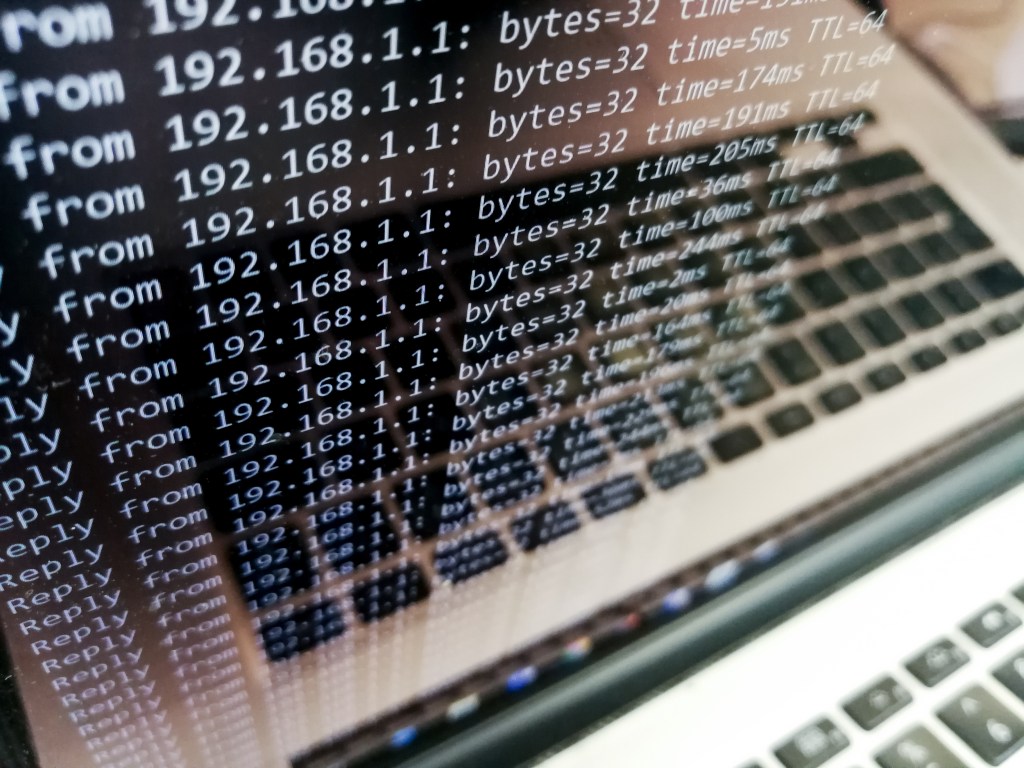
DDoS attacks are a significant threat to internet security that disrupt normal traffic by overwhelming servers. Identifying and mitigating DDoS attacks is crucial. Detection involves monitoring traffic patterns, analyzing sources, and using Intrusion Detection Systems. Mitigation strategies include blackhole routing, rate limiting, Web Application Firewall, and Anycast network diffusion. Netizen offers advanced security solutions and…
-

A recent Windows zero-day vulnerability (CVE-2024-38193) was exploited by North Korea’s Lazarus APT group, allowing the installation of the FudModule rootkit. This advanced breach highlights the urgent need for organizations to apply patches promptly and strengthen their security measures to combat increasingly sophisticated cyber threats. Netizen offers advanced security solutions and support services.
-

OpenAI recently shut down an Iranian influence campaign called Storm-2035, using ChatGPT to sway opinions on US political issues and global events. Flint, Michigan suffered a ransomware attack, affecting online services. Amid these challenges, Netizen offers advanced security solutions, compliance support, and automated assessment tools to protect IT infrastructure and mitigate risks.
-

The cybersecurity industry continues to experience rapid growth, driven by the increasing frequency and sophistication of cyber threats. For those looking to start a career in this field, there are numerous entry-level opportunities that offer a solid foundation and promising career trajectory. This guide provides an overview of some common entry-level cybersecurity roles, highlighting key…
-

Firewalls are essential for data protection. Next Generation Firewalls (NGFWs) go beyond traditional firewalls, offering advanced features like application control, intrusion prevention, and cloud-delivered threat intelligence. NGFWs provide comprehensive security, addressing modern cyber threats effectively. While traditional firewalls have their place, NGFWs are superior for robust network protection in today’s digital landscape.
-

Large language models like GPT-4 raise concerns as they can autonomously exploit cybersecurity vulnerabilities, posing a significant threat. These AI advancements may enhance defense measures but also empower malicious actors. The cybersecurity community must proactively develop defensive measures and regulate the deployment of these models to mitigate potential risks.
-

Microsoft’s August 2024 Patch Tuesday addresses 89 security flaws, with 8 critical vulnerabilities in various categories. Six zero-day vulnerabilities were actively exploited, including local privilege escalation flaws and remote code execution issues. Adobe also released 11 security bulletins for its products. Prompt installation of updates is crucial, with backup recommended as a precaution.
-

A cybersecurity breach at National Public Data has exposed 2.7 billion records of US citizens, leading to a class-action lawsuit. The lawsuit argues the company failed to protect personal information and benefited economically from collecting it. Malicious browser extensions have also been identified as a new vector for malware distribution, affecting at least 300,000 users.…
-

KnowBe4, a cybersecurity firm, faced a security breach involving a North Korean hacker posing as an employee. Although no data was compromised, the incident prompted tighter hiring and vetting processes. Organizations can prevent insider threats by implementing end-user training, UEBA tools, MFA, network segmentation, monitoring, incident response, and clear policies. Netizen offers advanced cybersecurity solutions…
-

The Policy Enforcement Point (PEP) is a crucial part of the Attribute-Based Access Control (ABAC) architecture, ensuring consistent access control and security for enterprise data. It intercepts user requests, evaluates attributes, and communicates with the Policy Decision Point (PDP) to determine access, providing robust security for modern applications.