Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
about
Category: CyberSecurity
-

Microsoft’s September 2024 Patch Tuesday addresses a total of 79 vulnerabilities, including actively exploited zero-day vulnerabilities. The critical updates primarily focus on remote code execution (RCE) and elevation of privilege (EoP) flaws. Adobe also released updates to address vulnerabilities across its product line. Users are encouraged to stay up-to-date with security patches and follow best…
-

Today’s Topics: CISA Responds to Controversial ‘Airport Security Bypass’ Vulnerability In late August 2024, cybersecurity researchers Ian Carroll and Sam Curry revealed a potentially alarming security flaw within FlyCASS, a third-party web-based application utilized by smaller airlines as part of the Cockpit Access Security System (CASS) and Known Crewmember (KCM) programs. These programs play a…
-

When evaluating ISO 27001 and ISO 27002, it’s essential to understand their distinct roles and purposes in the realm of information security management. Although both standards are closely related, they serve different functions, and recognizing these differences can help you implement them more effectively. General Differences ISO 27001 and ISO 27002 have distinct objectives, which…
-

The National Institute of Standards and Technology (NIST) has recently unveiled three new Federal Information Processing Standards (FIPS) aimed at addressing the emerging challenges posed by quantum computing. These standards—FIPS 203, 204, and 205—represent a pivotal advancement in strengthening the resilience of digital communications against future quantum threats, while also bolstering current cryptographic practices. Overview…
-
Volt Typhoon, a Chinese state-sponsored hacking group, has emerged as a significant player in global cybersecurity, focusing particularly on critical infrastructure. This detailed analysis explores Volt Typhoon’s operations, the impacts of its activities, and how we can effectively defend against such threats. Understanding these aspects is crucial for protecting national security and maintaining global stability.…
-

Security vulnerabilities are a significant concern for businesses. Netizen’s Security Operations Center (SOC) has identified five critical vulnerabilities in popular software and platforms, emphasizing the importance of prompt patching. These vulnerabilities enable remote attackers to execute arbitrary code, manipulate critical data, and disrupt system availability. Netizen offers advanced security solutions to protect businesses from such…
-

This content covers phishing tactics targeting Amazon users, EU scrutiny of Meta, and a federal recovery from a CrowdStrike outage. It advises caution with unsolicited links and attachments, scrutinizing messages, and not divulging personal information online. It also highlights Netizen’s cybersecurity solutions including CISO-as-a-Service and vulnerability assessments.
-
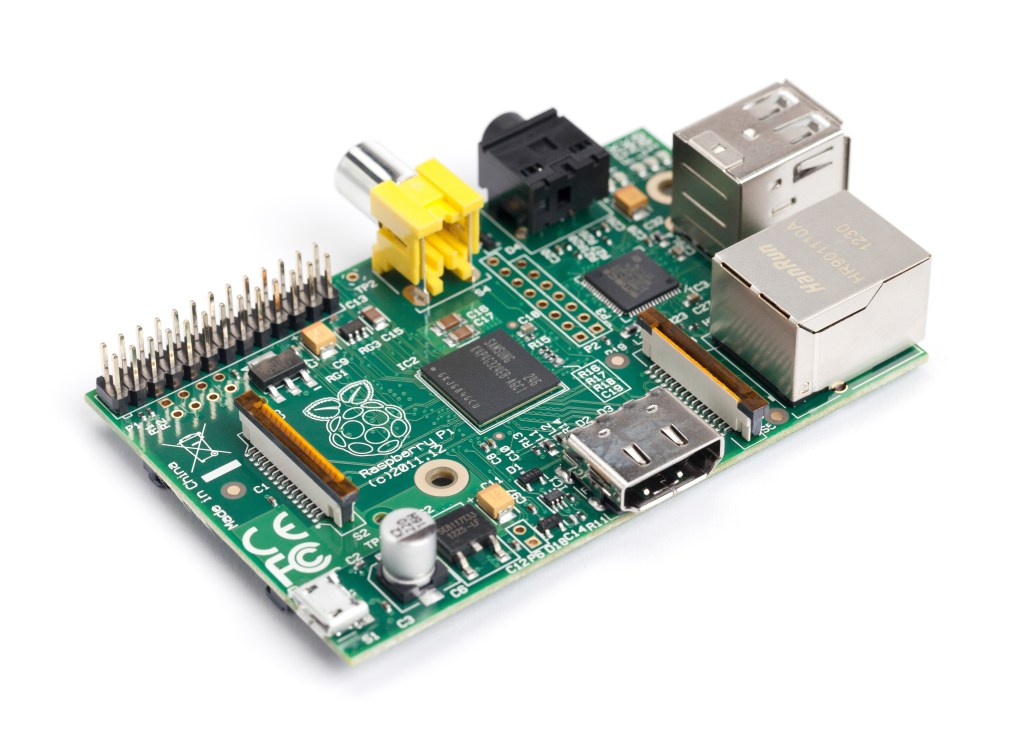
Penetration testing is a flexible skill for cybersecurity analysts. A drop box, like the one built with a Raspberry Pi 3 and TP-Link AC1300 Wi-Fi adapter, provides secure, cost-effective, and easy network access. Netizen offers cybersecurity services, including penetration testing, vulnerability assessments, and automation tools. Visit www.netizen.net/contact for inquiries.
-

A newly discovered vulnerability in Microsoft 365 Copilot highlights how attackers can leverage advanced techniques, such as prompt injection and ASCII smuggling, to exfiltrate sensitive user data. This issue has raised serious concerns in the cybersecurity world, especially considering the rapid integration of AI tools into enterprise environments. The Exploit Breakdown This vulnerability, disclosed to…
-

The FBI’s shortcomings in securing sensitive storage media were exposed in an OIG audit, indicating improper handling and storage of decommissioned devices. Meanwhile, Pavel Durov, CEO of Telegram, was arrested in France for alleged failure to moderate criminal activities on the platform.