Netizen Blog and News
The Netizen team sharing expertise, insights and useful information in cybersecurity, compliance, and software assurance.
recent posts
about
Category: Application Security
-

ChatGPT’s Atlas browser combines browsing with an LLM, increasing security risks via prompt injection vulnerabilities. It blurs boundaries between browsing functions and language processing, exposing users to potential operational threats. Enhanced control measures are crucial for organizations adopting agent-based systems, necessitating least-access permissions, sandbox execution, and rigorous authentication processes.
-
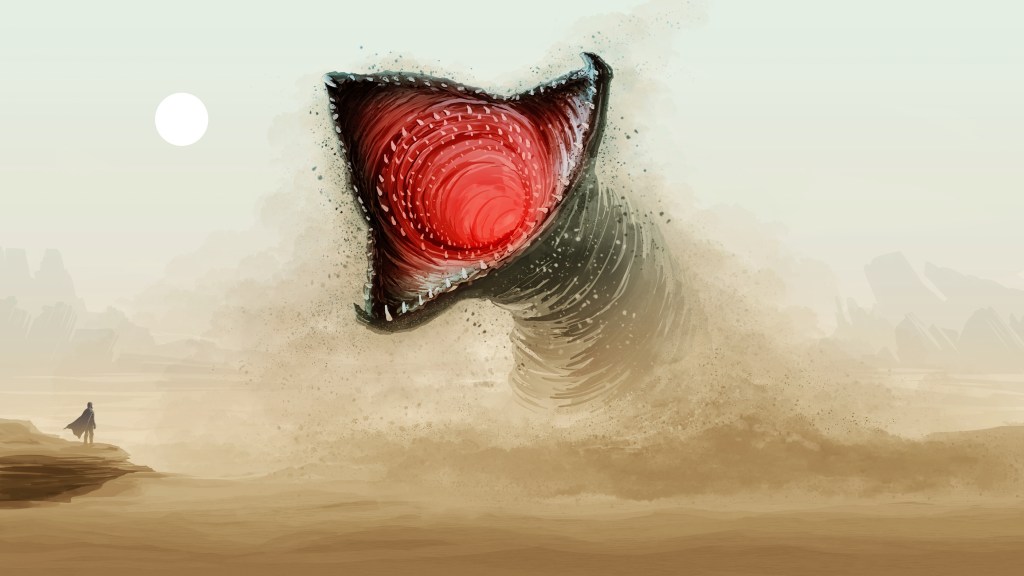
A surge of malicious activity in the npm ecosystem re-emerged on November 24, linked to the Shai Hulud campaign. The attack targets gaps in authentication token migration, potentially compromising developer environments. Hundreds of packages were affected, prompting organizations to audit dependencies, rotate credentials, and enhance security measures to mitigate risks associated with exposed secrets.
-

Recent cyber threats include a flaw in 7-Zip’s symbolic link processing, tracked as CVE-2025-11001, and a Salesforce supply-chain breach involving Gainsight, which allowed OAuth token theft. Organizations are encouraged to update software and establish clear access policies for third-party integrations to mitigate risks and enhance cybersecurity. Netizen offers solutions for secure IT infrastructure.
-

The integration of AI in DevOps is revolutionizing software development, yet presents governance challenges in regulated environments. Issues like accountability for AI-generated code, compliance with security policies, and potential liabilities must be addressed. Organizations need robust validation processes to ensure compliance and maintain audit readiness in AI-enhanced development pipelines.
-

In September 2025, AI-driven cyber espionage was revealed as a significant global threat, with a Chinese group autonomously infiltrating organizations using Anthropic’s Claude Code model. Concurrently, Amazon identified attacks exploiting zero-day vulnerabilities in Cisco and Citrix systems, emphasizing the need for enhanced network security and monitoring against advanced threats in identity infrastructures.
-

DNS security, often overlooked in cybersecurity discussions, is critical as it translates URLs into IP addresses. Attackers exploit its trust-based system through various methods, such as hijacking and tunneling. Organizations must enhance DNS defenses by implementing DNSSEC, monitoring traffic, and ensuring compliance with frameworks like CMMC 2.0 to safeguard sensitive information.
-

Security Operations Centers (SOCs) traditionally relied on static indicators of compromise, which have become ineffective against rapidly evolving threats. Transitioning to intent-based detection allows SOCs to focus on an attacker’s objectives rather than specific tools, enhancing threat detection and response. This shift involves adopting behavioral analytics and improving collaboration with threat intelligence teams.
-

A new wave of phishing attacks, utilizing ClickFix pages and PureRAT malware, targets hotel booking accounts, compromising systems and stealing credentials. Microsoft warns about Whisper Leak, a privacy threat that exposes AI chatbot conversation topics despite encryption. Businesses are urged to bolster cybersecurity and assess their defenses against these threats.
-

Cyber risk management has evolved, necessitating Continuous Threat Exposure Management (CTEM) to address modern challenges. CTEM proactively identifies, validates, and mitigates digital exposures across various environments. It extends beyond traditional vulnerability management by encompassing all risk factors, enhancing governance, risk, and compliance programs, and fostering ongoing organizational resilience against evolving threats.
-

Patch management is crucial for cybersecurity, yet organizations often face patch lag due to conflicting IT goals and legacy systems. Delays can lead to significant vulnerabilities and compliance issues, while attackers exploit known flaws quickly. Continuous patching and risk-based approaches are necessary. Netizen offers proactive services to enhance patch management and security effectiveness.